|
By Al Pessin
Pentagon 10 March 2006 More than 260 doctors from around the world have called on the U.S. military to stop force-feeding detainees at the Guantanamo detention center who are on a hunger strike. The doctors signed a letter published Friday in the respected British medical journal "Lancet." But at the Pentagon, a spokesman says there is no plan to review what he calls the "involuntary" feeding, which he says is done only when "appropriate or medically necessary."
The doctors' letter says force-feeding is a violation of declarations by the World Medical Association, documents it says the American Medical Association has signed. The American Medical Association is the largest association of physicians in the United States, and it is generally recognized as the arbiter of medical ethics issues for American doctors. The association's own ethical guidelines say doctors should respect a person's decision to refuse to eat, as long as that person is mentally competent and understands the consequences of the decision. "The law is that prisoners have a right to refuse any treatment, and physicians have to respect that informed decision that those individuals have consented to," said Richard Horton, editor of the Lancet journal. "So anything that breaches that informed decision is not defensible in law." The letter in Lancet calls on the U.S. government to end force-feeding and allow independent physicians to assess the condition of the Guantanamo detainees. Defense Department spokesman Bryan Whitman says there is no plan to review the policy. "The policy of the department is unchanged," he said. "And it is to support the preservation of life by appropriate clinical means, and to do that in a humane manner." Lawyers for detainees say the few remaining on hunger strike have been subjected to inhumane treatment. The lawyers say their clients have been strapped to chairs and had feeding tubes forced through their noses and down their throats. The lawyers claim that the doctors at Guantanamo changed their approach earlier this year, removing and re-inserting the tubes for each feeding, making the process much more painful for the detainees, and causing many of them to abandon the hunger strike. A senior U.S. general acknowledged last month that chairs are used to restrain detainees who resist the tube feeding. According to the U.S. military, the hunger strike began last August and reached a high of 84 detainees in December. Detainees were demanding freedom, or at least some indication of when and under what circumstances they might be released. Officials say there is a review process for that, but lawyers for the detainees say it is not a legal process. By January, officials said the number of detainees on hunger strike was down to 15. Spokesman Bryan Whitman says there are now six men on hunger strike, and three of them are being fed against their will. Officials say only those whose health deteriorates significantly are force fed. Still, Whitman acknowledges the issue of force-feeding is a difficult one. "I think it's fair to say that these are difficult issues," he said. "They're difficult moral, ethical, legal issues. And one would not expect that everyone would come to a consensus on this. The department has not come by this policy without a lot of deliberate consideration, deliberation and has determined that this is the appropriate way forward at this time." But the Lancet editor, Richard Horton, says if the U.S. government ignores calls to end the force-feeding, it is violating international law. "They have an international legal obligation to take notice of this," he said. "If they choose not to, they're breaking international law." The letter in Lancet says the appropriate medical governing bodies should discipline U.S. doctors who participate in force-feeding. U.S. military doctors at Guantanamo say they provide "compassionate and consistent" care to the detainees, and that resistance to the tube feeding has eased as a result. |
|
By LILA RAJIVA
Counterpunch 10 Mar 06 A year of stonewalling a Freedom of Information lawsuit by the Associated Press and now the Pentagon releases documents (Friday, March 3, 2006) with the names of hundreds of detainees held at Guantanamo.
The more than five thousand pages give us a flavor of the eclectic--ragtag, might be a better word--mix of prisoners in the Cuban camp and the equally varied treatment they received. The British Guardian-- from a keen sense of fair play, one supposes--devotes a column to telling us that after all, yes, there were two young boys who actually had a good time of it-- said good time running to movies, books, and soccer games. That wipes the slate clean on Abu Ghraib, see? It would be interesting to know more about those two .... and about the many more boys who didn't exactly get such Eagle Scout treatment, but what we'd really like to know is why we get a breathless column devoted to this reassuring anomaly but no one sees fit to give equal time to any of the three hundred other prisoners who testify to goings on a tad less pleasant. The hitherto nameless three hundred turn into recognizable characters in these new documents. There are goat herds and shopkeepers; there is the Taliban cook carrying a radio and hand grenades, the Iraqi millionaire who worked for MI5--only they deny it--and the Afghan farmer clinging to his rifle and his frontier freedom like a Montana militiaman cornered by the Feds. There are the metals cages made from discarded shipping containers --six by six, exposed to sun and rain--in which the prisoners were caged 24/7 and let out, shackled, only to use the toilet. There were the regular and severe punishments doled out for infractions as senseless as having an extra cup in the cage. (1) But--except for one--the most important characters in this squalid drama are a no-show in the press. And that exception--Major Geoffrey Miller--doesn't get the star billing he deserves, either. One: Miller It was Miller who was behind the aggressive psychological tactics used at Gitmo between 2002 and 2004--where military interrogators posing as FBI agents, gift-wrapped suspects in the Israeli flag and forced others to watch homosexual porn under strobe lights in 18 hour interrogation sessions (Feb. 23, 2006). It was Miller who overrode FBI warnings that information gathered by illegal techniques would be inadmissible in court. It was also Miller who was sent from Cuba to Iraq to "Gitmoize" interrogation. It was only after Miller's first visit to Abu Ghraib in August 2003 that the guards began siccing the dogs on prisoners, torturing them sexually, and attacking their religious beliefs. (2) Here's Jack Reed (D-RI) on the timeline: "General Miller came to Iraq in August...He also recommended the establishment of a theater joint interrogation and detention center...That's August, and then October we start seeing a series of abusive behaviors, which the accused [the military police and their commander, Janis Karpinski] suggest were a result of encouragement or direction from these intelligence people in this theater joint interrogation and detention center." (3) Even after the Abu Ghraib report broke and we were told piously by Mr. Rumsfeld that the system would be fixed ASAP, it was Miller who was sent back again to take care of things. Doesn't the man merit at least one fawning newspaper column for his original contributions to moral suasion? Or for his well-documented animus against Muslims? Take Muslim prison chaplain, Capt. James "Yousef" Yee. In 2002 Miller accused Yee of espionage and detained him for 76 days in shackles and solitary confinement for the most part. When no evidence of guilt turned up, the charges were first reduced to mishandling classified information and lying to investigators, and then dropped completely, but instead of apologizing, Miller rapped Yee on tangential charges of adultery and possession of pornography--charges meant only to humiliate him and his family. They were also finally overturned. (4) Who would put such a spiteful bigot in charge of interrogating Muslim prisoners? Two: Boykin The same folks, apparently, who picked General William "Jerry" Boykin to be Deputy Under Secretary for Defense in October 2003, precisely around the time the Abu Ghraib abuses were taking place. What does Boykin, a militant evangelical Christian think of Muslims? Let's see: In dress uniform and polished jump boots, he told a religious group in Oregon in June that same year that radical Islamists hate the United States "because we're a Christian nation, because our foundation and our roots are Judeo-Christian ... and the enemy is a guy named Satan." Recounting a Special Ops mission against a Muslim warlord in Somalia, he informed another audience, "I knew my God was bigger than his. I knew that my God was a real God and his was an idol." In 2002, he stated, "We in the army of God, in the house of God, kingdom of God have been raised for such a time as this," and at least once said of President Bush: "He's in the White House because God put him there." (5) Add to this a resume studded with every rash Special Ops mission in recent memory--from the hunt for Columbian drug kingpin, Pablo Escobar, to the bungled Iran hostage rescue, and you get the picture of a man who likes death- or-glory escapades. Especially ones signed off on by Jehovah and aimed at Muslims. In fact, a Crusader--and not a very competent one. Is there any proof that Boykin had anything to do with Abu Ghraib? Plenty. Boykin played a key role in the counter-insurgency campaign that escalated from 2003 on and is known to have reviewed Israeli tactics used in the assault on the Palestinian refugee camp in Jenin in 2002. Any resemblance between American actions in Iraq and Israeli actions in Palestine is, of course, completely coincidental and not even remotely related to the question of why we might have a broad policy of detaining Muslims and subjecting them to futuristic forms of torture Boykin was also one of the key planners of the new Special Forces group--Task Force 121- intended to wipe out the Iraqi resistance through targeted assassinations similar to the Phoenix Program in Vietnam. Nice prep work for the man who also just happens to be the person responsible for briefing Undersecretary for Defense Stephen Cambone on what Miller was upto at Abu Ghraib. (6) Boykin is Cambone's top aide. Three: Cambone Which brings us to Cambone. What did he know? Nothing much, according to his testimony at the Senate Hearings. On issue after issue, the man saw no evil and heard no evil: "Until the pictures began appearing in the Press, sir, I had not sense of that scope or scale." [about the torture photos which the Army began investigating in January, five months before the story broke] And about the extent to which the CIA was involved in interrogations: "I didn't make a connection in the sense there was a significant issue here....Furthermore, I still don't know that there is a significant issue here.." Cambone also claimed not to have seen Red Cross reports or repeated complaints to Bremer and Rice in 2003. Nor was he briefed by General Miller on his August visit to Iraq. The mantra is always the same--"I am not aware," "as best I know," "that's about the extent of my knowledge." (7) And since we presume a minimum of intelligence in our defense officials, we can't even chalk this up to imbecility. Then why the stone-walling? Simple. Military Intelligence and the CIA (both operating extensively through creme de la creme special forces units and out of control private contractors) are at the heart of the torture policy.... which is itself at the heart of the entire counter-terrorist strategy.... which is in turn the lynch pin of the war on terror. Counter terrorism today--from what we know of such units as Rumsfeld's P2OG (Proactive, Preemptive Operations Group)--is modeled after the Gladio-type forces that ran the so-called "Strategy of Tension in Europe" in the aftermath of the Cold War and were used extensively to stage covert provocations and false-flag operations meant to discredit socialism. So, trace Abu Ghraib back to MI and the CIA and Cambone knows you trace right it back to the people running the new Strategy of Tension....against the Muslim world. The people who have reframed real (and staged) terrorist acts as part of an endless World War IV --- while, not incidentally, standing to profit substantially from the reframing. You trace it back to defense contractors. You trace it back to the black heart of the Defense-Intelligence octopus. And where does Cambone fit in the octopus? As Under Secretary of Defense for Intelligence (USD-I), the civilian boss directly in charge of the entire system of information gathering, he's part of the brain. A big part. The position was created by Rumsfeld as recently as 2003 for the sole purpose of wrenching control of intelligence away from independent outfits (the DIA, the NSA, each armed service's intelligence unit) and housing it in the Pentagon under one roof. Moreover, Cambone, a ballistics missile and space weapons fanatic, had no background in intelligence and was hated by those who did. He was Rumsfeld's point man on RMA (Revolution in Military Affairs)--the Don's controversial transformation of the military. He was picked to steam roll any opposition by military men--and there was plenty of opposition. (8) As part of the RMA, raw (unanalyzed) intelligence is made available to the military--supposedly with rules governing its use....but who really believes that rules like that don't quickly fold when needed? The intelligence is gathered through "persistent surveillance" and uses such new technologies as Space-Based Radar. Turns out "persistent surveillance" is suspiciously similar to what goes on under Rumsfeld's little false-flag franchise, P20G. Indeed, in April 2003, Rumsfeld placed Cambone in charge of the counter-terrorism initiative coded "Grey Fox." Here are Cambone's own words with my emphasis in italics: "For the war fighter, it [Space-Based Radar] could support predictive battlespace awareness and could be equally predictive for the intelligence analyst. In other words, by finding the anomalous event, what you do is you get out ahead of activities. Your refresh rate, if you will, is such that you're not looking at history, you're looking at current events, and once you start looking at current events, as opposed to the history, your ability to start drawing those trend lines and anticipate how the subject of your inquiry is going to act and respond increases dramatically." (9) Preemptive intelligence, like preemptive war. Pick up people who might commit terrorist acts, not those who actually have. A perfect recipe for show trials and random street sweeps like the ones that gave us Abu Ghraib. And completely contradictory to the practice or theory of professional intelligence analysts. But, of course, Cambone, a graduate of the neo-conservative hotbed Claremont College, is not an analyst but an ideologue. An ideologue, who as USD-I gets his clammy hands on 85% of the intelligence budget versus the mere 12% under the director of central intelligence. Frankly, Cambone would had to have been consulted just for the money needed to insert private contractors and military intelligence into interrogation. Yet, at the Senate Hearings this all powerful czar swore up and down he knew nothing--nada, zip, zero, zilch--about Miller, about the Red Cross, about MI, about the dogs, about the pictures..... And a hypnotized media has never called him on that outrageous performance. Four: Feith Nor has there been a solitary twitter about the role of the enigmatic Douglas Feith, though he deserves it as much as Cambone. Until he left in early 2005, Feith was Cambone's opposite number at Defense as Under Secretary of Defense for Policy (USD-P), a post Cambone himself held earlier. If Cambone had the means to tamper with intelligence-gathering and interrogation, Feith had the motive. A vocal advocate of regime change in the Middle East long before 9-11, a hard-line Zionist hawk and member of ZOA (Zionist Organization of America), Feith's publicly expressed views are incendiary. He has stated that Oslo should be repudiated and the West Bank and Gaza reoccupied even if "the price in blood would be high" as "a necessary form of detoxification." (10) And his actions in government match. In 1982, he was investigated over allegations that he had handed over secret documents to the Israeli embassy and left the National Security Council under a cloud. Later, he was hired back by Richard Perle. On leaving the Pentagon in 1986, he promptly started a law firm in Israel. His partner at the time, Marc Zell, is a spokesman for the Jewish settlers' movement on the occupied West Bank. Yes--those settlers. (11) The ones several parasangs to the right of Ariel Sharon. Naturally--that would have nothing whatsoever to do with any opinions Feith might hold on Arabs, Iraq, or the proper way to chat with a manacled Muslim. In 2001, with the US economy in recession and financial crisis looming in the markets and neo-conservatives ensconced in power, friends began helping friends: Wolfowitz as Deputy Secretary of State brought Feith in at DOD, while Feith brought Perle to the Defense Policy Board and hired another favorite ideological hit man, Michael Ledeen, who also has a documented history of siphoning classified information to Israeli intelligence and selling sensitive military technology to China. Ledeen was hired by Feith at OSP to handle material requiring high-level security clearance. (12) And what does this cozy arrangement have to do with Abu Ghraib? Well--for a start, it blows a hole in the theory that rounding up a few Semitic goat-herds and housewives has anything to do with national security--at least in the common meaning of that term, to wit., refraining from selling out the interests of the nation-state to which one belongs by accident of birth, choice, or lack of initiative. Because it's quite clear from the action-packed resumes of the crew of transnational wheelers and dealers above, that national--or even international- security is the last thing on their minds. Feith has also been up to more institutionalized shenanigans: First, he was active in the controversial Defense Policy Board, whose former head Richard Perle resigned when conflicts of interest between his board duties and his business affairs came to light. Then, he was also boss at the Office of Special Plans, which "stove-piped" un-vetted or raw intelligence on Iraq directly (outside the normal channels, that is) to the White House. The objective was to buttress the administration's flimsy case for war. Which means that Feith was grasping for any wisp of straw when it came to intelligence. And so, had every incentive to get it for us whole-sale where he could most easily--on the Iraqi street. (13) And an important point. OSP, set up by Wolfowitz, had direct responsibility for detainee operations in Iraq. By dismissing the advice of Middle Eastern experts at the State Department on post-war planning, it contributed hugely to the failure of prison policy. OSP also oversaw reconstruction contracts--with all their outrageous bid-rigging and profiteering. And it did all of this through an institutional end-run around government. Yet, at the Senate Hearings, Cambone swore up and down that Feith was in the dark about Abu Ghraib and the Taguba report, although when the report actually came out, here's what Daniel Dunn, the top computer security officer in Feith's office had to say in an urgent email memo to Pentagon staff: "Information contained in this report is classified; do not go to FOX News to read or obtain a copy." (14) Sounds like at least one person knew that Feith had something to fear. And Feith himself quietly resigned last year, some say, because of yet another scandal--the Larry Franklin case. Franklin, convicted of espionage this year, worked for Feith at OSP in 2002 and 2003 and was sent abroad on sensitive missions--involving Iran-Contra figures-- aimed at pushing through the Iraq WMD hustle. Franklin pleaded guilty in January to passing information to Israel about U.S. policy towards Iran through the American Israel Public Affairs Committee (AIPAC), the foremost pro-Israel lobbying organization in the U.S. (15) So there you have it. Take two rancid Christian zealots and a half-pint of frothing Zionist fanaticism. Add to it a well-curdled neo-conservative ideologue and stir until bubbling in a Middle Eastern cauldron. Top with a generous helping of psycho-sexual sadism. And voila, Torture Imperial. Serves several thousands at a time. Miller, Boykin, Cambone, and Feith. Wolfowitz and Rumsfeld also, of course. Possibly, Rice and President Bush. But for now, these four will do. Lila Rajiva is a free-lance journalist and author of "The Language of Empire: Abu Ghraib and the American media," (Monthly Review Press). She can be reached at: lrajiva@hotmail.com Notes: (1) "In Guantanamo Bay Documents, Prisoners Plead for Release U.S. Makes First Public Accounting Of Detainees," Josh White and Julie Tate, Washington Post, March 5, 2006; Page A08. See also "Pentagon discloses names of Gitmo detainees," Miranda Leitsinger and Ben Fox, AP, March 4, 2006. (2) See "The Language of Empire: Abu Ghraib and the American Media," Lila Rajiva, MR Press, December 2005, p. 51. (3) Senate Armed Services Committee Hearing, May 11, 2004. (4) "How Dubious Evidence Spurred Relentless Guantánamo Spy Hunt," Tim Golden, New York Times, December 19, 2004. See also "Who Is Geoffrey Miller: Is the Man from Guantánamo the Right Man for Iraq?" Peter Ogden, Center for American Progress, May 17, 2004. (5) "General Casts War in Religious Terms," Richard T. Cooper, Los Angeles Times, October 16, 2003. (6) "Moving Targets: Will the counter-insurgency plan in Iraq repeat the mistakes of Vietnam?" Seymour Hersh, New Yorker, December 13, 2003. See also "US Israel trains US assassination squads in Iraq," Julian Borger, Guardian, 9 December 2003. (7) Senate Armed Services Committee Hearing, May 11, 2004. (8) In "The Secret World of Stephen Cambone: Rumsfeld's Enforcer," (Counterpunch, February 7, 2006), Jeffrey St. Clair writes that a Republican staffer on the Senate Foreign Relations Committee told CounterPunch that the little-known Cambone rivals Paul Wolfowitz in power at the Pentagon. "Cambone is a truly dangerous player," said the staffer." He is Rumsfeld's guard dog, implacably loyal. While Wolfowitz positions himself to step into the top spot should Rumsfeld get axed, Cambone has dug in and gone to war against the insurgents in the Pentagon. Cambone's fingerprints are all over the occupation and the interrogation scandal. For him, there's no turning back." St. Clair contends credibly that "Cambone's real mission was to keep tabs on Feith, a notorious hothead and Cheney loyalist whom Rumsfeld distrusts." (9) "Intelligence on demand: An interview with Stephen Cambone, undersecretary of defense for intelligence," Glenn W. Goodman, Jr., ISR Journal, December 1, 2003. http://www.defenselink.mil/usdi/camboneinterview.html (10) "A Dangerous Appointment," James Zogby, Washington Watch, April 16, 2001 (11) "Loss of Feith in Douglas," Jim Lobe, Inter Press Service, November 7, 2003. (Reprinted in Asia Times). (12) "Serving Two Flags: Neo-Cons, Israel and the Bush Administration," Stephen Green, Counterpunch, February 28/29, 2004. Again, one has to clearly distinguish between acceptable information sharing between two very close allies and the fine point at which something crosses that boundary. (13) "The new Pentagon papers: A high-ranking military officer reveals how Defense Department extremists suppressed information and twisted the truth to drive the country to war," Karen Kwiatkowski, Salon.com, March 10, 2004. (14) "The Israeli Torture Template: Rape, Feces and Urine-Dipped Cloth Sacks," Wayne Madsen, Counterpunch, May 10, 2004. (15) "Pentagon analyst indicted for leaks to Israel: a subterranean power struggle in Washington," Patrick Martin, World Socialist Web, 10 May 2005. |
|
by Bruce Schneier
Wired News Mar, 09, 2006 In the post-9/11 world, there's much focus on connecting the dots. Many believe data mining is the crystal ball that will enable us to uncover future terrorist plots. But even in the most wildly optimistic projections, data mining isn't tenable for that purpose. We're not trading privacy for security; we're giving up privacy and getting no security in return.
Most people first learned about data mining in November 2002, when news broke about a massive government data mining program called Total Information Awareness. The basic idea was as audacious as it was repellent: suck up as much data as possible about everyone, sift through it with massive computers, and investigate patterns that might indicate terrorist plots. Americans across the political spectrum denounced the program, and in September 2003, Congress eliminated its funding and closed its offices. But TIA didn't die. According to The National Journal, it just changed its name and moved inside the Defense Department. This shouldn't be a surprise. In May 2004, the General Accounting Office published a report (.pdf) listing 122 different federal government data-mining programs that used people's personal information. This list didn't include classified programs, like the NSA's eavesdropping effort or state-run programs like MATRIX. The promise of data mining is compelling, and convinces many. But it's wrong. We're not going to find terrorist plots through systems like this, and we're going to waste valuable resources chasing down false alarms. To understand why, we have to look at the economics of the system. Security is always a trade-off, and for a system to be worthwhile, the advantages have to be greater than the disadvantages. A national security data-mining program is going to find some percentage of real attacks and some percentage of false alarms. If the benefits of finding and stopping those attacks outweigh the cost -- in money, liberties, etc. -- then the system is a good one. If not, you'd be better off spending that capital elsewhere. Data mining works best when you're searching for a well-defined profile, a reasonable number of attacks per year and a low cost of false alarms. Credit-card fraud is one of data mining's success stories: all credit-card companies mine their transaction databases for data for spending patterns that indicate a stolen card. Many credit-card thieves share a pattern -- purchase expensive luxury goods, purchase things that can be easily fenced, etc. -- and data mining systems can minimize the losses in many cases by shutting down the card. In addition, the cost of false alarms is only a phone call to the cardholder asking him to verify a couple of purchases. The cardholders don't even resent these phone calls -- as long as they're infrequent -- so the cost is just a few minutes of operator time. Terrorist plots are different. There is no well-defined profile and attacks are very rare. Taken together, these facts mean that data-mining systems won't uncover any terrorist plots until they are very accurate, and that even very accurate systems will be so flooded with false alarms that they will be useless. All data-mining systems fail in two different ways: false positives and false negatives. A false positive is when the system identifies a terrorist plot that really isn't one. A false negative is when the system misses an actual terrorist plot. Depending on how you "tune" your detection algorithms, you can err on one side or the other: you can increase the number of false positives to ensure you are less likely to miss an actual terrorist plot, or you can reduce the number of false positives at the expense of missing terrorist plots. To reduce both those numbers, you need a well-defined profile. And that's a problem when it comes to terrorism. In hindsight, it was really easy to connect the 9/11 dots and point to the warning signs, but it's much harder before the fact. Certainly, many terrorist plots share common warning signs, but each is unique, as well. The better you can define what you're looking for, the better your results will be. Data mining for terrorist plots will be sloppy, and it'll be hard to find anything useful. Data mining is like searching for a needle in a haystack. There are 900 million credit cards in circulation in the United States. According to the FTC September 2003 Identity Theft Survey Report, about 1 percent (10 million) cards are stolen and fraudulently used each year. When it comes to terrorism, however, trillions of connections exist between people and events -- things that the data-mining system will have to "look at" -- and very few plots. This rarity makes even accurate identification systems useless. Let's look at some numbers. We'll be optimistic -- we'll assume the system has a one in 100 false-positive rate (99 percent accurate), and a one in 1,000 false-negative rate (99.9 percent accurate). Assume 1 trillion possible indicators to sift through: that's about 10 events -- e-mails, phone calls, purchases, web destinations, whatever -- per person in the United States per day. Also assume that 10 of them are actually terrorists plotting. This unrealistically accurate system will generate 1 billion false alarms for every real terrorist plot it uncovers. Every day of every year, the police will have to investigate 27 million potential plots in order to find the one real terrorist plot per month. Raise that false-positive accuracy to an absurd 99.9999 percent and you're still chasing 2,750 false alarms per day -- but that will inevitably raise your false negatives, and you're going to miss some of those 10 real plots. This isn't anything new. In statistics, it's called the "base rate fallacy," and it applies in other domains as well. For example, even highly accurate medical tests are useless as diagnostic tools if the incidence of the disease is rare in the general population. Terrorist attacks are also rare, any "test" is going to result in an endless stream of false alarms. This is exactly the sort of thing we saw with the NSA's eavesdropping program: the New York Times reported that the computers spat out thousands of tips per month. Every one of them turned out to be a false alarm. And the cost was enormous -- not just for the FBI agents running around chasing dead-end leads instead of doing things that might actually make us safer, but also the cost in civil liberties. The fundamental freedoms that make our country the envy of the world are valuable, and not something that we should throw away lightly. Data mining can work. It helps Visa keep the costs of fraud down, just as it helps Amazon alert me to books I might want to buy and Google show me advertising I'm more likely to be interested in. But these are all instances where the cost of false positives is low (a phone call from a Visa operator or an uninteresting ad) in systems that have value even if there is a high number of false negatives. Finding terrorism plots is not a problem that lends itself to data mining. It's a needle-in-a-haystack problem, and throwing more hay on the pile doesn't make that problem any easier. We'd be far better off putting people in charge of investigating potential plots and letting them direct the computers, instead of putting the computers in charge and letting them decide who should be investigated. |
|
By Tim Shorrock
The Nation March 9, 2006. Two months after the New York Times revealed that the Bush Administration ordered the National Security Agency to conduct warrantless surveillance of American citizens, only three corporations--AT&T, Sprint and MCI--have been identified by the media as cooperating. If the reports in the Times and other newspapers are true, these companies have allowed the NSA to intercept thousands of telephone calls, fax messages and e-mails without warrants from a special oversight court established by Congress under the 1978 Foreign Intelligence Surveillance Act (FISA).
Some companies, according to the same reports, have given the NSA a direct hookup to their huge databases of communications records. The NSA, using the same supercomputers that analyze foreign communications, sifts through this data for key words and phrases that could indicate communication to or from suspected terrorists or terrorist sympathizers and then tracks those individuals and their ever-widening circle of associates. "This is the US version of Echelon," says Albert Gidari, a prominent telecommunications attorney in Seattle, referring to a massive eavesdropping program run by the NSA and its English-speaking counterparts that created a huge controversy in Europe in the late 1990s. So far, a handful of Democratic lawmakers--Representative John Conyers, the ranking Democrat on the House Judiciary Committee, and Senators Edward Kennedy and Russell Feingold--have attempted to obtain information from companies involved in the domestic surveillance program. But they've largely been rebuffed. Further details about the highly classified program are likely to emerge as the Electronic Frontier Foundation pursues a lawsuit, filed January 31, against AT&T for violating privacy laws by giving the NSA direct access to its telephone records database and Internet transaction logs. On February 16 a federal judge gave the Bush Administration until March 8 to turn over a list of internal documents related to two other lawsuits, filed by the American Civil Liberties Union and the Electronic Privacy Information Center, seeking an injunction to end the program. Despite the President's rigorous defense of the program, no company has dared to admit its cooperation publicly. Their reticence is understandable: The Justice Department has launched a criminal investigation of the government officials who leaked the NSA story to the Times, and many constitutional scholars and a few lawmakers believe the program is both illegal and unconstitutional. And the companies may be embarrassed at being caught--particularly AT&T, which spent millions advertising its global services during the Winter Olympics. "It's a huge betrayal of the public trust, and they know it," says Bruce Schneier, the founder and chief technology officer of Counterpane Internet Security, a California consulting firm. Corporations have been cooperating with the NSA for half a century. What's different now is that they appear to be helping the NSA deploy its awesome computing and data-mining powers inside the United States in direct contravention of US law, which specifically bans the agency from collecting information from US citizens living inside the United States. "They wouldn't touch US persons before unless they had a FISA warrant," says a former national security official who read NSA intercepts as part of his work for the State Department and the Pentagon. This is happening at a time when both the military and its spy agencies are more dependent on the private sector than ever before, and an increasing number of companies are involved. In the 1970s, when Congress acted to stop domestic spying programs like Operation Shamrock, in which the NSA monitored overseas telegrams and phone calls, the communications industry was in its infancy. "It was basically Western Union for cables, and AT&T for the telephone," says James Bamford, who revealed the existence of the NSA in his famous book The Puzzle Palace and is a plaintiff in the ACLU lawsuit. "It's much more complicated now." In fact, today's global telecom market includes dozens of companies that compete with AT&T, Sprint and MCI for telephone and mobile services, as well as scores of Internet service providers like Google, Yahoo! and AOL that offer e-mail, Internet and voice connections to customers around the world. They are served by multinational conglomerates like Apollo, Flag Atlantic and Global Crossing, which own and operate the global system of undersea fiber-optic cables that link the United States to the rest of the world. Any one of them could be among the companies contacted by intelligence officials when President Bush issued his 2002 executive order to obtain surveillance without FISA approval. Nobody's talking, though. Asked if AT&T, which was recently acquired by SBC Communications, is cooperating with the NSA, AT&T spokesman Walt Sharp said, "We don't comment on national security matters." He referred me to a recent AT&T letter to Representative Conyers, which stated that AT&T "abides by all applicable laws, regulations and statutes in its operations and, in particular, with respect to requests for assistance from governmental authorities." MCI, which was acquired in January by Verizon, and Sprint, which recently merged with Nextel Communications, declined to comment. Attorney Gidari, who has represented Google, T-Mobile, Nextel and Cingular Wireless (now part of AT&T), believes that "some companies, both telecom and Internet," were asked to participate in the NSA program. But he suggests that only a limited number agreed. "The list of those who said no is much longer than most people think," he says. The NSA, some analysts say, may have sought the assistance of US telecoms because most of the world's cable operators are controlled by foreign corporations. Apollo, for example, is owned by Britain's Cable & Wireless, while Flag Atlantic is owned by the Reliance Group of India. Much of the international "transit traffic" carried by the cable companies flows through the United States (this is particularly true of communications emanating from South America and moving between Asia and Europe). The NSA could get access to this traffic by sending a submarine team to splice the cables in international waters, as the agency once did to the Soviet Union's undersea military cables. But that is an extremely expensive proposition, and politically dicey to boot--which is where the US telecoms come in. "Cooperation with the telcos doesn't make NSA surveillance possible, but it does make it cheaper," says Schneier, the technology consultant. According to Alan Mauldin, a senior research analyst with TeleGeography Research in Washington, DC, it would be possible for US intelligence operatives to gain access to transit traffic from anywhere in the country with the cooperation of a US company. "You could be inland, at an important city like New York or Washington, DC, where networks interconnect, and you could have the ability to tap into the whole network for not only that city but between that city and the rest of the world," he says. Foreign-owned cable operators, says Gidari, are also required by US law to maintain security offices manned by US citizens, with background checks and security clearances at the landing sites in Oregon, Florida, New Jersey and other states where fiber-optic cables come ashore. The government has gone to great lengths to insure law-enforcement access to foreign-owned telecom companies. Take the example of Global Crossing, which owns several undersea cable systems and claims to serve more than 700 carriers, mobile operators and ISPs. Three years ago, as Global Crossing was emerging from one of the largest bankruptcies in US history, it was purchased by ST Telemedia, which is partly owned by the government of Singapore. As part of the US approval process (which occurred at a time when Global Crossing was being advised by Richard Perle, then-chairman of Donald Rumsfeld's Defense Policy Board), the company signed an unprecedented Network Security Agreement with the FBI and the Defense Department. Under the agreement, which is on file with the Federal Communications Commission, Global Crossing pledged that "all domestic communications" would pass through a facility "physically located in the United States, from which Electronic Surveillance can be conducted pursuant to lawful US process." (Global Crossing declined to comment.) Legal experts say the wording is significant in the context of the NSA spying flap, but cautioned not to read too much into it. "These agreements are not uncommon in the industry," says James Andrew Lewis, director of the Technology and Public Policy Program at the Center for Strategic and International Studies in Washington. "They provide assurances that US interests won't suffer damage with foreign ownership." History proves a good guide to how the NSA would go about winning cooperation from a telecom company. When telephone and telegraph companies began assisting the NSA during the 1940s, only one or two executives were in on the secret. That kind of arrangement continued into the 1970s, and is probably how cooperation with the NSA works today, says Kenneth Bass III, a Justice Department official during the Carter Administration. "Once the CEO approved, all the contacts [with the intelligence agencies] would be worked at a lower level," he says. "The telcos have been participating in surveillance activities for decades--pre-FISA, post-FISA--so it's nothing new to them." Bass, who helped craft the FISA law and worked with the NSA to implement it, adds that he "would not be surprised at all" if cooperating executives received from the Bush Administration "the same sort of briefing, but much more detailed and specific than the FISA court got when [the surveillance] was first approved." For US intelligence officials looking for allies in the industry, AT&T, MCI and Sprint have a lot to offer. In 2002, when the spying program began, AT&T's CEO was C. Michael Armstrong, the former CEO of Hughes Electronic Corp. At the time, Armstrong was also chairman of the Business Roundtable's Security Task Force, where he was instrumental in creating CEO COM LINK, a secure telecommunications system that allows the chief executives of major US corporations to speak directly to senior members of Bush's Cabinet during national emergencies. Randall Stephenson, a former SBC Communications executive who is now AT&T's chief operating officer, is a member of the National Security Telecommunications Advisory Committee, a group of executives from the communications and defense industries who advise the President on security issues related to telecom. Those executives, all of whom hold security clearances, meet at the White House once a year--Vice President Cheney was the speaker at their last meeting--and hold quarterly conference calls with high-ranking officials. (Asked if the NSA surveillance was ever discussed at these sessions, committee spokesman Stephen Barrett said, "We do not participate in intelligence gathering.") AT&T also makes no bones about its national security work. When SBC was preparing to acquire the company last year, the two companies underscored their ties with US intelligence in joint comments to the FCC. "AT&T's support of the intelligence and defense communities includes the performance of various classified contracts," the companies said, pointing out that AT&T "maintains special secure facilities for the performance of classified work and the safeguarding of classified information." MCI, too, is a major government contractor and was highly valued by Verizon in part because of its work in defense and intelligence. Nicholas Katzenbach, the former US Attorney General who was appointed chairman of MCI's board after the spectacular collapse of its previous owner, WorldCom, reiterated MCI's intelligence connections in a 2003 statement to the Senate Judiciary Committee. "We are especially proud," he wrote, "of our role in supporting our national-security agencies' infrastructure, and we are gratified by the many positive comments about our service from officials at the US Department of Defense and other national-security agencies." MCI's general counsel--who would presumably have a say in any decision to cooperate with the NSA--is William Barr. He is a former assistant general counsel at the Central Intelligence Agency and served as Attorney General during the Administration of President George H.W. Bush. Sprint Nextel is top-loaded with executives with long experience in national security and defense. Chairman and CEO Gary Forsee is a member of Bush's telecom council (as is Lawrence Babbio, the vice chairman and president of Verizon). Keith Bane, a company director, recently retired from a twenty-nine-year career with Motorola, which has worked closely with US intelligence for decades. William Conway Jr. and former FCC chairman William Kennard are managing directors of the Carlyle Group, the Washington private equity fund that invests heavily in the military and has extensive contacts in the Bush Administration. There's another group of companies, largely overlooked, that could also be cooperating with the NSA. These are firms clustered around the Beltway that contract with the agency to provide intelligence analysts, data-mining technologies and equipment used in the NSA's global signals-intelligence operations. The largest of them employ so many former intelligence officials that it's almost impossible to see where the government ends and the private sector begins. Booz Allen Hamilton, the prime contractor for Trailblazer, a huge NSA project updating its surveillance and eavesdropping infrastructure, employs several NSA alumni, including Mike McConnell, its vice president, who retired as NSA director in 1996. (Ralph Shrader, the company's CEO, joined Booz Allen in 1978 after serving in senior positions with Western Union and RCA, both of which cooperated with the NSA on Operation Shamrock.) SI International, a software and systems engineering company with NSA contracts, recently hired Harry Gatanas, the NSA's former director of acquisitions and outsourcing, to oversee its $250-million-a-year business with US intelligence and the Pentagon. Science Applications International Corporation, another big NSA contractor, is run by executives with long histories in military intelligence, including COO Duane Andrews, a former Assistant Secretary of Defense for Command, Control, Communications and Intelligence. Are firms that cooperate with the NSA legally culpable? Bamford, who is not a lawyer but probably knows more about the NSA than any American outside government, says yes. "The FISA law is very clear," he says. "If you don't have a warrant, you're in violation, and the penalty is five years and you can be sued by the aggrieved parties." Kevin Bankston, an attorney for the Electronic Frontier Foundation, adds that US law "not only prohibits unauthorized wiretapping; it also prohibits unauthorized disclosure or use of illegally wiretapped information. As long as you were doing that, you're potentially liable." Schneier, the technology consultant, harbors no doubts either. "Arguing that this is legal is basically saying we're in a police state." But Gidari, the Seattle telecom attorney, believes that companies would be insulated from legal challenges if they had assurances from the government that the program was within the law. He also says Congress has passed legislation granting immunity to companies operating under "statutory grants of authority" from the government. "It's not a slamdunk, but it is a good-faith defense," he says. Former Justice Department official Bass agrees but says reliance on oral requests from US officials is another matter: "If they didn't get the type of legal assurances the FISA provides for"--such as a written statement from the Attorney General--"there could be some legal exposure." But a full airing of the legal issues raised by the surveillance program may be a long time coming. "The likelihood of any enforcement absent a change in administration is zero," Bass says. |
|
MSNBC and NBC News
March 10, 2006 The Department of Defense admitted in a letter obtained by NBC News on Thursday that it had wrongly added peaceful demonstrators to a database of possible domestic terrorist threats. The letter followed an NBC report focusing on the Defense Department's Threat and Local Observation Notice, or TALON, report.
Acting Deputy Undersecretary of Defense Roger W. Rogalski's letter came in reply to a memo from Sen. Patrick Leahy, D-Vt., who had demanded answers about the process of identifying domestic protesters as suspicious and removing their names when they are wrongly listed. "The recent review of the TALON Reporting System ... identified a small number of reports that did not meet the TALON reporting criteria. Those reports dealt with domestic anti-military protests or demonstrations potentially impacting DoD facilities or personnel," Rogalski wrote on Wednesday. "While the information was of value to military commanders, it should not have been retained in the Cornerstone database." Threats directed against Defense Department In 2003, the Defense Department directed a little-known agency, Counterintelligence Field Activity (CIFA), to establish and "maintain a domestic law enforcement database that includes information related to potential terrorist threats directed against the Department of Defense." Then-Deputy Secretary of Defense Paul Wolfowitz also established TALON at that time. The original NBC News report, from December, focused on a secret 400-page Defense Department document listing more than 1,500 "suspicious incidents" across the country over a 10-month period. One such incident was a small group of activists meeting in a Quaker Meeting House in Lake Worth, Fla., to plan a protest against military recruiting at local high schools. In his Wednesday letter, Rogalski said such anomalies in the TALON database had been removed. "They did not pertain to potential foreign terrorist activity and thus should never have been entered into the Cornerstone database. These reports have since been removed from the Cornerstone database and refresher training on intelligence oversight and database management is being given," Rogalski wrote. Rogalski said only 43 names were improperly added to the database, and those were from protest-related reports such as the Quaker meeting in Florida. "All reports concerning protest activities have been purged," the letter said. TALON reports provide "non-validated domestic threat information" from military units throughout the United States that are collected and retained in the Cornerstone CIFA database. The reports include details on potential surveillance of military bases, stolen vehicles, bomb threats and planned antiwar protests. In the program's first year, the agency received more than 5,000 TALON reports. Nearly four dozen antiwar meetings listed The Defense Department document provides an inside look at how the U.S. military has stepped up intelligence gathering since 9/11. The database includes nearly four dozen antiwar meetings or protests, including some that have taken place far from any military installation, post or recruitment center, according to NBC News' Lisa Myers, who first wrote about the story in December. Among those listed were a large antiwar protest in Los Angeles in March 2004 that included effigies of President Bush and antiwar protest banners, a planned protest against military recruiters in December 2004 in Boston, and a planned protest in April 2004 at McDonald's National Salute to America's Heroes - a military air and sea show in Fort Lauderdale, Fla. The Fort Lauderdale protest was deemed not to be a credible threat, and a column in the database concludes: "U.S. group exercising constitutional rights." Two-hundred and forty-three other incidents in the database were discounted because they had no connection to the Department of Defense - yet they all remained in the database. |
|
by Spero News
10 Mar 06 Bernice Lalo says the Shoshone Nation is being "threatened by extinction." But a landmark decision Friday by a UN committee is causing some Western Shoshone's to have hope,
The United States was urged to "freeze", "desist" and "stop" actions being taken or threatened to be taken against the Western Shoshone Peoples of the Western Shoshone Nation, in a Friday decision by the UN Committee on the Elimination of Racial Discrimination (CERD). The U.S. has until July 15, 2006 to provide the UN committee with information on the action it had taken. This action challenges the US government's assertion of federal ownership of nearly 90 percent of Western Shoshone lands. "The mines are polluting our waters, destroying hot springs and exploding sacred mountains-our burials along with them--attempting to erase our signature on the land," says Lalo. "We are coerced and threatened by mining and Federal agencies when we seek to continue spiritual prayers for traditional food or medicine on Shoshone land." According to Lalo, "We have endured murder of our Newe people for centuries, as chronicled in military records, but now we are asked to endure a more painful death from the U.S. governmental agencies -- a separation from land and spiritual renewal." The decision expressed particular concern that the U.S.' basis for claiming federal title to Western Shoshone land rests on a theory of "gradual encroachment" through a "compensation" process in the Indian Claims Commission. Joe Kennedy, also a Western Shoshone insists that "we have rights to protect our homelands and stop the destruction of our land, water, and air by the abuses of the United States government and the multinational corporations. He says "the situation is outrageous and we're glad the United Nations Committee agrees with us." "Our people have suffered more nuclear testing than anywhere else in the world and they're continuing underground testing despite our protests. Yucca Mountain is being hollowed out in order to store nuclear waste. We cannot stand for it," Kennedy claims, adding "this earth, the air, the water are sacred. People of all races must stop this insanity now in order to secure a safe future for all." The decision is historic in that it is the first time a United Nations Committee has issued a full decision against the U.S. in respect to its highly controversial Federal Indian law and policy. CERD stressed the "nature and urgency" of the Shoshone situation informing the U.S. that it goes "well beyond" the normal reporting process and warrants immediate attention under the Committee's Early Warning and Urgent Action Procedure. The land base covers approximately 60 million acres, stretching across what is now referred to as the states of Nevada, Idaho, Utah and California. Western Shoshone rights to the land -- which they continue to use, care for, and occupy today -- were recognized by the United States in 1863 by the Treaty of Ruby Valley. The U.S. now claims these same lands as "public" or federal lands through an agency process and has denied Western Shoshone fair access to U.S. courts through that same process. The land base has been and continues to be used by the United States for military testing, open pit cyanide heap leach gold mining and nuclear waste disposal planning. The U.S. has engaged in military style seizures of Shoshone livestock, trespass fines in the millions of dollars and ongoing armed surveillance of Western Shoshone who continue to assert their original and treaty rights. "While others are allowed the freedom of religion, we are kept from the very same right. The Newe (people) use this ancestral land for sacred ceremonies. The federal agencies prevent our access to some of these important areas. Our ancestors' burials are being dug up and placed into local museums' basement storage areas because of surge of gold mines and nuclear developments. This is an outrage to our people," said Judy Rojo. "We pray for the healing of our peoples, the land and the harassment and destruction to stop." Steven Brady, also a Western Shoshone, said that "this battle has been going on for quite some time, but we've seen a dramatic increase in the federal government and the companies' rush to finalize what they consider a settlement in order to get a hold of our lands for activities that are contaminating our water and our air." Based upon these actions and a dramatic escalation of new actions threatening irreparable harm to Western Shoshone and their environment, last year, with the support of the Univ. of Arizona Indigenous Law and Policy Program, the Western Shoshone filed a renewed legal action at the United Nations CERD. In addition to evidence, the Western Shoshone delegation also delivered over 13,000 signatures from citizens across the United States of America supporting the Western Shoshone action to CERD. This petition was a result of a campaign organized by the rights-based development organization Oxfam America to demonstrate the widespread concern for the Western Shoshone peoples to the United Nations. CERD rejected the U.S.' argument that the situation was not "novel" and therefore should wait to be reviewed until the U.S. submits its Periodic Report -- past due since 2003. The Committee informed the U.S. that "(a)lthough these are indeed long-standing issues...they warrant immediate and effective action... (and) should be dealt with as a matter of priority." The United States was "urged to pay particular attention to the right to health and cultural rights of the Western Shoshone...which may be infringed upon by activities threatening their environment and/or disregarding the spiritual and cultural significance they give to their ancestral lands." CERD presented its decision to the Western Shoshone this morning. The decision details the U.S.' actions against the Western Shoshone and calls upon the United States to immediately: -- Respect and protect the human rights of the Western Shoshone peoples; -- Initiate a dialogue with the representatives of the Western Shoshone peoples in order to find a solution acceptable to them, and which complies with their rights; -- Adopt the following measures until a final decision or settlement is reached on the status, use and occupation of Western Shoshone ancestral lands in accordance with due process of law and the U.S.' obligations under the Convention; -- Freeze all efforts to privatize Western Shoshone ancestral lands for transfer to multinational extractive industries and energy developers; -- Desist from all activities planned and/or conducted on Western Shoshone ancestral lands; -- Stop imposing grazing fees, livestock impoundments, hunting, fishing and gathering restrictions and rescind all notices already made. The decision highlights that this same process was found by the Inter-American Commission on Human Rights to violate "international human rights norms, principles and standards that govern determination of indigenous property interests." When the U.S. last appeared before the Committee in 2001, Committee members expressed alarm and concern that U.S. laws regarding indigenous peoples continue to be based on the outdated, colonial era "doctrine of discovery." The decision issued today demonstrates a solid commitment by the United Nations human rights system to make the Western Shoshone's struggle a priority. Whereas indigenous peoples have been active at the United Nations for several decades, the decision today also brings a breath of hope to indigenous communities across the U.S. and globally where the negative effects of U.S. policy and influence reach. In its decision, the Committee drew particular attention to its General recommendation 23 (1997) on the rights of indigenous peoples, in particular their right to own, develop, control and use their communal lands, territories and resources. "The Western Shoshone Nation is very thankful to the Committee members for their decision affirming U.S. discrimination and destructive policies do not go on unaccounted for. Truth is what it is -- that can never change," said Judy Rojo. |
|
Steve Watson
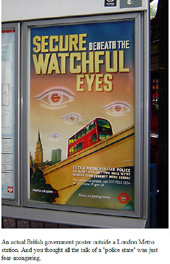
Infowars March 8 2006 In a world where the perception is the reality, all countries need to have the capability to manage their own perceptual alignment otherwise someone else will. We live in a global village, which is reliant on communication and perception. Every country needs the tools to be part of that game.
A direct quote from the website of Strategic Communication Laboratories, a London based company that offers "the most powerful weapon in the world", the ability to manage every aspect of a conflict from one operation centre. Take a look around their website and witness sickening quote after quote explaining how their vision is to allow the total control of citizens by their government or their military, to keep it that way, and to facilitate conflicts with and the takeover of other countries and the execution of total control over their citizens. The idea put across by SCL is that if you can control the perceptions people have of reality, then you can control reality itself. As the world moves further away from the 20th century concept of the Cold War, it becomes increasingly clear that the very nature of warfare itself has changed. The old style conflicts were about overpowering the enemy and winning ground. The new wars are about ideas, belief systems and ideologies. The battle is no longer about winning territory; it is about winning minds. George Orwell was right on the money when he envisaged the coming 21st century as a battle based on the PERCEPTION of reality. in 1984, his classic warning to the world, Orwell told us that we would have to face this threat: The Party said that Oceania had never been in alliance with Eurasia. He, Winston Smith, knew that Oceania had been in alliance with Eurasia as short a time as four years ago. But where did that knowledge exist? Only in his own consciousness, which in any case must soon be annihilated. And if all others accepted the lie which the Party imposed -if all records told the same tale -- then the lie passed into history and became truth. 'Who controls the past,' ran the Party slogan, 'controls the future: who controls the present controls the past.' And yet the past, though of its nature alterable, never had been altered. Whatever was true now was true from everlasting to everlasting. It was quite simple. All that was needed was an unending series of victories over your own memory. 'Reality control', they called it: in Newspeak, 'doublethink'. - George Orwell, 1984, Chapter 3 (1948) SCL's vision is no different from the constructed artificial reality designed to house the minds of the human race portrayed in the feature film The Matrix. If you present all the people with a fabricated collective illusion of reality, and enough meaningless distractions, they may stop questioning that reality when things don't seem to add up. Formed in 1993, SCL's customers include NGOs, police departments, military forces, municipal authorities, and the UN. According to the website, funding for SCL has been provided by a number of "private high net worth individuals" all based in the UK. The company has invested nearly $20 million into research at what they call the Behavioural Dynamics Institute (BDi), the world's leading authority on persuasion, communication psychology and public diplomacy. Given that they are the "World's leaders" it is strange that they do not have a website. SCL is about selling to the military and Governments, or those that wish to control the military and the Government, the tools that they need to fight and the win the information war for people's minds. Within its OpCentres are all the tools needed to initiate an elite full spectrum police state takeover - reality control. The SCL website makes the following chilling statement: The last 5 years have seen a flurry of Homeland Security scenarios enacted and re-enacted on the streets of our cities. What if there is a biological attack, or the detonation of multiple explosive devices? However, a major flaw has emerged in many of the scenarios - the unmanageability of civilians. They do not behave as they are supposed to. When a virus hits a city, civilians do not line up for vaccination: they run for the hills. When terrorists are looking for a target, it is the predictability of civilian behaviour that makes the terrorists' job easier. What if there was a way to control civilian behaviour when it counts? Imagine the benefits of having civilians as cooperating partners. Strategic Communication makes the people part of the solution, not part of the problem. But how do the so-called OpCentres provide the ability to do this? Well according to SCL: An Opcentre puts influence, control and power back into the hands of the government and military, giving them greater power to influence the enemy in time of conflict and enhanced access to their citizens during a crisis. For instance, an Opcentre can be designed to override all national radio and TV broadcasts, allowing the government and military to communicate with the public as the need arises. The OpCentres allow for powerful PSYOP campaigns to be conducted, which can engender support within the national community for proposed military action or more bone chillingly, "develop national resilience and behavioural compliance for homeland security issues". They also allow for the takeover and control of Financial markets, health ministries, and foreign affairs. Modules within the Opcentres can range from "Word-of Mouth Units" to "Cultural Alignment Units" and previous projects SCL have undertaken for clients include to "Design and develop a permanent military strategic communication facility capable of delivering strategic and operational psyop campaigns for a South Asian country." and to "Design, build and install a Homeland Security Centre for an Asian country. The Opcentre can override all national radio and TV broadcasts in time of crisis." Internal security issues are covered too, with the ability within the OpCentre to quell public unrest, manage large crowds or riot situations, prevent insurgency and other such public affairs crises under the umbrella of a "counter-terrorism programme." Almost every country suffers from some problematic faction within its citizens. These disaffected groups may be driven by religious fervour, self-importance or just greed. In all cases, their ability to operate and recruit new members depends on the perceptual environment and the levels of tolerance of the state and its citizens. SCL specialises in producing solutions for governments so that they can significantly increase their control and management of disaffected groups as part of a wider counter-terrorism programme. According to SCL, although it offers solutions for all departments of government, it "makes sense" to give total control of of their installations to the Head of State because other ministers of government may be "over zealous" or may not share the same vision. Perhaps there may be some ministers who are not hell bent on destroying the freedoms of everyone and perpetuating endless psy-war on people and nations all over the planet? hmmm? Perhaps? This is the future of the globalist police state takeover, they have the infrastructure in place, they have the ability to initiate the takeover NOW. However, they recognise that perception is everything and we are engaged within an INFOWAR. They could not takeover tomorrow because not enough people would believe the perception of reality that they are transmitting. Currently we are in the majority, they still have a long way to go before their PSYOPS campaigns and "word of mouth units" can do an effective enough job. Of course the main task currently assigned to the "Cultural Alignment Unit" is to create the perception that we are the minority, and that anyone who is not with the Government is with the "disaffected groups" more widely referred to as "the terrorists" We are holding them off by spreading the truth and defending our freedoms in our own peaceful revolution of information. It is our reality that is at stake, they want to control our reality with conflict and disharmony and therefore they must continue to create the perception that that is the way the world is. As SCL puts it on their own website: We live in a world of communication, where perception is very often the reality. Those individuals that control the perceptions are the ones that control virtually everything. Most modern conflicts are based on misaligned perceptions, ideologies, opinions about religion, etc. If a government does not have the tools to manage the perceptions which effect security, defence, finance, tourism, health and foreign relations, then it may well find itself at the mercy of those that do. We respond with the words of Orwell in 1984: Being a minority, even a minority of one, did not make you mad. There was truth and there was untruth, and if you clung to the truth even against the whole world, you were not mad. The obvious, the silly, and the true had to be defended. Truisms are true, hold on to that! The solid world exists, its laws do not change. Stones are hard, water is wet, objects unsupported fall towards the earth's centre. With the feeling that he was speaking directly to O'Brien, and also that he was setting forth an important axiom, Winston wrote: Freedom is the freedom to say that two plus two make four. If that is granted, all else follows. Contact SCL here Here is what it says in the company overview: Strategic Communication Laboratories is the leading supplier of strategic communications, information operations and public diplomacy to governments and military clients around the world. The company is the exclusive licence holder of the BDi strategic communication methodology, which is the most advanced and effective persuasion methodology for social and group communication. The company provides solutions mainly for defence, internal security and foreign affairs governmental departments, but also provides solutions for tourism, financial markets & investment and health programmes. SCL operates throughout the world and is based in London, UK. The Head Office employs about 30 people and there maybe as many as 2000 specialists employed on projects worldwide. The company was formed in 1993 and produced a number of projects for the Behavioural Dynamics Institute, which was undergoing development trials for its methodology. The successful outcome of the trials led to the permanent association of SCL and BDi. Today SCL is not only the unique licence holder of the BDi methodology, but more importantly, after 12 years, it is the only team fully trained in its operation. |
|
By DAVID D. KIRKPATRICK
and SCOTT SHANE March 8, 2006 WASHINGTON - Moving to tamp down Democratic calls for an investigation of the administration's domestic eavesdropping program, Republicans on the Senate Intelligence Committee said Tuesday that they had reached agreement with the White House on proposed bills to impose new oversight but allow wiretapping without warrants for up to 45 days.
The agreement, hashed out in weeks of negotiations between Vice President Dick Cheney and Republicans critical of the program, dashes Democratic hopes of starting a full committee investigation because the proposal won the support of Senators Chuck Hagel of Nebraska and Olympia J. Snowe of Maine. The two, both Republicans, had threatened to support a fuller inquiry if the White House did not disclose more about the program to Congress. "We are reasserting Congressional responsibility and oversight," Ms. Snowe said. The proposed legislation would create a seven-member "terrorist surveillance subcommittee" and require the administration to give it full access to the details of the program's operations. Ms. Snowe said the panel would start work on Wednesday, and called it "the beginning, not the end of the process." "We have to get the facts in order to weigh in," she said. "We will do more if we learn there is more to do." The agreement would reinforce the authority of the Foreign Intelligence Surveillance Court, which was created in 1978 to issue special warrants for spying but was sidestepped by the administration. The measure would require the administration to seek a warrant from the court whenever possible. If the administration elects not to do so after 45 days, the attorney general must certify that the surveillance is necessary to protect the country and explain to the subcommittee why the administration has not sought a warrant. The attorney general would be required to give an update to the subcommittee every 45 days. Democrats called the deal an abdication of the special bipartisan committee's role as a watchdog, saying the Republicans had in effect blessed the program before learning how it worked or what it entailed. "The committee is, to put it bluntly, basically under the control of the White House," said Senator John D. Rockefeller IV, the West Virginia Democrat who is vice chairman of the panel. The House Intelligence Committee said last week that it would seek limited briefings for some panel members so that they could weigh changes to the Foreign Intelligence Surveillance Act, but the Republican leaders of the House committee stopped far short of proposing the kind of continuing oversight and rules changes that the Senate committee has settled on. A spokeswoman for the White House, Dana Perino, called the Republican senators' proposal "a generally sound approach." "We're eager to work with Congress on legislation that would further codify the president's authority," Ms. Perino said. "We remain committed to our principle, that we will not do anything that undermines the program's capabilities or the president's authority." Republicans on the committee, however, emphasized the administration's resistance to the accord. Senator Pat Roberts, the Kansas Republican who is chairman of the Intelligence Committee and helped broker the deal, called it "the agreement we insisted upon." Ms. Snowe said the proposal had met "considerable reluctance" from the White House in negotiations. The committee had scheduled a vote on a full investigation for Tuesday afternoon if there was no accord with the White House to disclose more about the program. As of midday, no resolution had been reached. Mr. Hagel said the group worked out the last-minute deal in long telephone calls with Mr. Cheney; the White House counsel, Harriet E. Miers; and Stephen J. Hadley, the assistant to the president for national security. The proposed bill would allow the president to authorize wiretapping without seeking a warrant for up to 45 days if the communication under surveillance involved someone suspected of being a member of or a collaborator with a specified list of terrorist groups and if at least one party to the conversation was outside the United States. The administration has provided some information in confidential briefings to a "Gang of Eight" lawmakers made up of the Republican and Democratic leaders of the House and the Senate, as well as their respective Intelligence Committees. Republican sponsors of the proposal said the new subcommittees would greatly improve lawmakers' ability to obtain digest information because the staffs for the first time would have access to it. Senator Mike DeWine, the Ohio Republican who helped draft the proposal, said it would bring the program "into the normal oversight of the Senate intelligence committee." But Senator Ron Wyden, Democrat of Oregon, compared the proposed bill to a doctor's diagnosis of an unexamined patient. "Congress doesn't have that great a history in reforming programs it knows a lot about," Mr. Wyden said. "Here Congress is trying to legislate in the dark." Senator Bill Frist, Republican of Tennessee, the majority leader, issued a statement supporting the proposal. It is not clear whether all the Republican critics will back the deal. Senator Arlen Specter, the Pennsylvania Republican who is chairman of the Senate Judiciary Committee, has said Congress should seek a court ruling on the legitimacy of the program in addition to new oversight. In a separate Senate committee hearing on Tuesday, Mr. Specter said, "We're having quite a time in getting responses to questions as to what has happened with the electronic surveillance program." He said he put the administration "on notice" he might seek to block its financing if Attorney General Alberto R. Gonzales did not give more information. Mr. Specter said in statement later that he hoped for a solution that would avoid resorting to such an extreme action. |
|
By John Leo
5 Mar 06 Law professor Eugene Volokh calls it "censorship envy." Muslims in Europe want the same sort of censorship that many nations now offer to other aggrieved groups. By law, 11 European nations can punish anyone who publicly denies the Holocaust. That's why the strange British historian David Irving is going to prison. Ken Livingstone, the madcap mayor of London, was suspended for four weeks for calling a Jewish reporter a Nazi. A Swedish pastor endured a long and harrowing prosecution for a sermon criticizing homosexuality, finally beating the rap in Sweden's Supreme Court.
Much of Europe has painted itself into a corner on the censorship issue. What can Norway say to pro-censorship Muslims when it already has a hate speech law forbidding, among other things, "publicly stirring up one part of the population against another," or any utterance that "threatens, insults or subjects to hatred, persecution or contempt any person or group of persons because of their creed, race, color or national or ethnic origin ... or homosexual bent"? No insulting utterances at all? Since most strong opinions can be construed as insulting (hurting someone's feelings), no insults means no free speech. It's not just Europe. In Canada, a teacher drew a suspension for a letter to a newspaper arguing that homosexuality is not a fixed orientation, but a condition that can be treated. He was not accused of discrimination, merely of expressing thoughts that the state defines as improper. Another Canadian newspaper was fined 4,500 Canadian dollars for printing an ad giving the citations -- but not the text -- of four biblical quotations against homosexuality. As David Bernstein writes in his book "You Can't Say That!": "It has apparently become illegal in Canada to advocate traditional Christian opposition to homosexual sex." Many nations have set themselves up for Muslim complaints by adopting the unofficial slogan of the West's chattering classes: Multiculturalism trumps free speech. Sensitivity and equality are viewed as so important that the individual right to speak out is routinely eclipsed. Naturally enough, Muslims want to play the same victim game as other aggrieved groups. The French Council of Muslims says it is considering taking France Soir, which reprinted the Danish cartoons, to court for provocation. In truth, Muslims have been playing the game for some time. Michel Houellebecq, a French novelist, said some derogatory things about the Quran. Muslim groups hauled him into court, but the novelist was eventually exonerated. Actress Brigitte Bardot, an animal rights activist, criticized Muslim ritual slaughter and was fined 10,000 francs for the offense. Italian journalist Oriana Fallaci wrote an angry anti-Muslim book, meant to waken the West to the gravity of the threat posed by Islam. Muslims pressed for her prosecution in France. The case was thrown out of court on a technicality in 2002, but she is scheduled to go on trial again this coming June. In Australia, a state tribunal found two pastors guilty of vilification of Muslims. They had argued that Islam is inherently a violent religion, and that Islam plans to take over Australia. To avoid a fine of up to 7,000 Australian dollars or three months in jail, they were ordered to apologize and to promise not to repeat their remarks anywhere in Australia or over the Internet. The pastors refused to comply and are appealing to the Supreme Court. The case has become a major cause, with churches and Christian leaders fighting to overturn the law, and Muslims pushing for a broad hate-speech law. An obvious thing to say about laws that limit speech is that we have no evidence that they work to meet their stated goal -- reducing bigotry and increasing tolerance. Banning Holocaust denial, on grounds that it is inherently anti-Semitic, has no track record of improving respect for Jews. If anything, hatred of Jews appears to be on the rise in these nations. Setting up certain groups as beyond criticism is bound to increase resentment among those not similarly favored. (Yes, we know all groups are supposed to be treated alike, but that is not the way these laws work.) In real life, the creation of protected classes sharpens intergroup tensions and leads to competition for victim status. An even more obvious point: We are very lucky to have the First Amendment. Without it, our chattering classes would be falling all over themselves to ban speech that offends sensitive groups, just like many Eurochatterers are doing now. We know this because our campus speech codes, the models for the disastrous hate-speech laws in Europe, Canada and Australia, were the inventions of our own elites. Without a First Amendment, the distortions and suppressions of campus life would likely have gone national. No more speech codes, please. In America, we get to throw rocks at all ideologies, religious and secular, and we get to debate issues, not have them declared off limits by sensitivity-prone agents of the state. |
|
by Robert Perry
10 Mar 06 Despite a dip in his opinion polls, George W. Bush's transformation of the United States into an authoritarian society continues apace, with new "compromises" with Congress actually consolidating his claims to virtually unlimited executive power.
Bush's latest success came as part of a supposed "concession" to Congress that would grant two new Republican-controlled seven-member subcommittees narrow oversight of Bush's warrantless wiretapping of Americans. While "moderate" Republican senators Mike DeWine of Ohio, Olympia Snowe of Maine, and Chuck Hagel of Nebraska hailed the plan as a retreat by the White House, the deal actually blesses Bush's authority to bypass the courts in spying on Americans and imposes on him only a toothless congressional review process. Indeed, the congressional plan may make matters worse, broadening the permissible scope of Bush's wiretaps to include Americans deemed to be "working in support of a terrorist group or organization." Given Bush's record of stretching words to his advantage and his claim that anyone who isn't "with us" is with the terrorists the vague concept of "working in support" could open almost any political critic of the Bush administration to surveillance. Plus, the only check on abuses would be the closed-door oversight work of the seven-member panels, which would only be informed of a warrantless wiretap after it had been in place for 45 days. Republicans also would have four of the seven seats on each subcommittee and any dissent from the minority Democrats would be kept secret. In other words, the plan would let Bush and his Republican congressional loyalists conduct wiretaps of anyone whose activities might be called supportive of terrorists, while any Democratic critic would be muzzled from saying anything publicly under penalty of law. Chilling Powers Under such an arrangement, it would not be difficult to envision the wiretapping of journalists writing critical articles about the abuse of terrorism suspects, or of disarmament experts who disagree with Bush's claims about some "rogue" state's weapons of mass destruction, or of a political rival who challenges Bush's interpretation of his Commander-in-Chief powers. Indeed, many Bush supporters have lobbed accusations of "treason" against the likes of journalist Seymour Hersh, weapons inspector Scott Ritter and former Vice President Al Gore because they have presented information that clashes with Bush's agenda. Other influential Republicans, such as Sen. Lindsey Graham of South Carolina, have urged Bush to move aggressively against suspected "fifth columnists" inside the United States who supposedly sympathize with the enemy. Graham also has called on Bush to use high-tech surveillance techniques to "map the battlefield electronically," which in the Internet Age means going beyond assessing the physical battlefield to examine the political connections among potential enemies so they can be neutralized at a time of crisis. "Here's where I think I'm your biggest fan," Graham told Attorney General Alberto Gonzales during Senate Judiciary Committee hearings on Feb. 6. "During the time of war, the administration has the inherent power, in my opinion, to surveil the enemy and to map the battlefield electronically not just physical, but to electronically map what the enemy is up to by seizing information and putting that puzzle together. "And the administration has not only the right, but the duty, in my opinion, to pursue Fifth Column movements," Graham said. "I stand by this President's ability, inherent to being Commander in Chief, to find out about Fifth Column movements, and I don't think you need a warrant to do that." Though the Bush administration has denied abusing its four-year-old warrantless wiretapping program, it has been unwilling to give details about the numbers of people swept up in the surveillance or define the precise criteria for who's wiretapped. Bush has insisted that the wiretaps are limited to the international communications of people in the United States who have gotten calls from al-Qaeda or its affiliates. Newspaper investigations, however, indicate the spying is much more extensive than Bush has admitted. The New York Times and the Washington Post have reported that the wiretapping by the National Security Agency has scooped up communications from thousands of innocent Americans. [See Consortiumnews.com's "Talkin' Texan Means Lyin' Big."] Investigation Blocked Congressional Democrats have called for an investigation to ascertain the scope of the warrantless wiretaps before addressing the administration's assertion that the 1978 Foreign Intelligence Surveillance Act doesn't give the nation's spy agencies the flexibility they need. But congressional Republicans and the White House torpedoed plans for an investigation and instead began drafting legislation that would effectively endorse Bush's claim to an unfettered right to bypass the Fourth Amendment's requirement of a court order before a legal search can be conducted. The new legislation, sponsored by Sen. DeWine, would permit the N.S.A. to intercept international phone calls and e-mails of U.S. residents if the administration saw "probable cause to believe that one party to the communication is a member, affiliate, or working in support of a terrorist group or organization." [NYT, March 9, 2006] After 45 days, the law would require the Attorney General to take one of three steps: end the wiretap, get a warrant from the secret FISA court, or inform the new oversight panels about the wiretap. White House spokesman Dana Perino said the administration was willing to give the new seven-member panels information about the wiretaps but that the members would be prohibited from divulging what they learn. [Washington Post, March 9, 2006] Congressional Democrats have criticized the DeWine plan as insufficient to prevent violations of civil liberties. Sen. John D. Rockefeller IV of West Virginia, the ranking Democrat on the Senate Intelligence Committee, said Congress first needed to exercise its responsibility to conduct oversight of the Executive Branch. "It is 'undersight' when they tell us what they want us to know," Rockefeller told the Washington Post. "It's 'oversight' when we know enough to ask our own questions." However, with hard-line Republicans like Senate Intelligence Committee Chairman Pat Roberts of Kansas joining with more moderate Republicans like Snowe and Hagel, the Democrats appear to have been out-flanked and out-muscled again. A similar process occurred in December 2005 when Congress passed legislation outlawing cruel, inhuman and degrading treatment of detainees in U.S. custody. But an amendment, promoted by Graham and co-sponsored by Sen. Carl Levin, D-Mich., limited legal appeals that Guantanamo Bay inmates could make in U.S. courts. Bush administration lawyers have since gone into federal court, citing the Graham-Levin amendment to prevent Guantanamo detainees from stopping alleged torture. In other words, the anti-torture law is being interpreted as granting Bush the sole right to decide how to interpret its provisions and when to enforce them. [For details, see Consortiumnews.com's "Bush Flummoxes Kafka, Orwell."] The legislation on warrantless wiretaps now promises to be the next White House "concession" that will, in reality, consolidate Bush's autocratic power in what looks like an inexorable march toward an end of the American democratic Republic. Originally published at (c) www.consortiumnews.com Robert Parry broke many of the Iran-Contra stories in the 1980s for the Associated Press and Newsweek. His latest book, Secrecy & Privilege: Rise of the Bush Dynasty from Watergate to Iraq, can be ordered at secrecyandprivilege.com. It's also available at Amazon.com, as is his 1999 book, Lost History: Contras, Cocaine, the Press & 'Project Truth.' |
Have a question or comment about the Signs page? Discuss it on the Signs of the Times news forum with the Signs Team.
Some icons appearing on this site were taken from the Crystal Package by Evarldo and other packages by: Yellowicon, Fernando Albuquerque, Tabtab, Mischa McLachlan, and Rhandros Dembicki.
Remember, we need your help to collect information on what is going on in your part of the world!
Send your article suggestions to: 
Contact Webmaster at signs-of-the-times.org
Cassiopaean materials Copyright ©1994-2014 Arkadiusz Jadczyk and Laura Knight-Jadczyk. All rights reserved. "Cassiopaea, Cassiopaean, Cassiopaeans," is a registered trademark of Arkadiusz Jadczyk and Laura Knight-Jadczyk.
Letters addressed to Cassiopaea, Quantum Future School, Ark or Laura, become the property of Arkadiusz Jadczyk and Laura Knight-Jadczyk
Republication and re-dissemination of our copyrighted material in any manner is expressly prohibited without prior written consent.
The Gladiator: John Fitzgerald Kennedy
John F. Kennedy and All Those "isms"
John F. Kennedy, J. Edgar Hoover, Organized Crime and the Global Village
John F. Kennedy and the Psychopathology of Politics
John F. Kennedy and the Pigs of War
John F. Kennedy and the Titans
John F. Kennedy, Oil, and the War on Terror
John F. Kennedy, The Secret Service and Rich, Fascist Texans
Recent Articles:
New in French! La fin du monde tel que nous le connaissons
New in French! Le "fascisme islamique"
New in Arabic! العدوّ الحقيقي
New! Spiritual Predator: Prem Rawat AKA Maharaji - Henry See
Top Secret! Clear Evidence that Flight 77 Hit The Pentagon on 9/11: a Parody - Simon Sackville
Latest Signs of the Times Editorials
Executing Saddam Hussein was an Act of Vandalism
Latest Topics on the Signs Forum |
Signs Monthly News Roundups!
June 2005
July 2005
August 2005
September 2005
October 2005
November
2005
February 2006
March 2006
April 2006
May 2006
June 2006
July 2006
August 2006
September 2006



![Validate my Atom 1.0 feed [Valid Atom 1.0]](/signs/images/valid-atom.png)