|
BY JOSH GERSTEIN
Staff Reporter of the Sun 28 Feb 06 Two federal judges in Florida have upheld the authority of individual courts to use the Patriot Act to order searches anywhere in the country for e-mails and computer data in all types of criminal investigations, overruling a magistrate who found that Congress limited such expanded jurisdiction to cases involving terrorism.
The disagreement among the jurists about the scope of their powers simmered for more than two years before coming to light in an opinion unsealed earlier this month. The resolution, which underscored the government's broad legal authority to intercept electronic communications, comes as debate is raging over President Bush's warrantless surveillance program and the duties of Internet providers to protect personal data. A magistrate judge in Orlando, James Glazebrook, first questioned the so-called nationwide-search provision in 2003, after investigators in a child pornography probe asked him to issue a search warrant requiring a "legitimate" California-based Web site to identify all users who accessed certain "password-protected" photos posted on the site. The Web provider was not named in public court records. Magistrate Glazebrook said that in passing the Patriot Act, formally known as the Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism Act, Congress made clear its focus was on terrorism. He said there was nothing in the language Congress adopted in the days after the September 11, 2001, terrorist attacks that suggested the nationwide-search provision should apply to garden variety federal cases. "The statutory language is clear and unambiguous in limiting district court authority to issue out-of-district warrants to investigations of terrorism, and that language controls this court's interpretation. The government has shown no legislative intent to the contrary," the magistrate wrote. He also noted that many of the examples given during legislative debate involved terrorism. The then chairman of the Senate Judiciary Committee, Senator Leahy, a Democrat of Vermont, described the nationwide-search language as applying in terrorism cases, the court noted. Magistrate Glazebrook denied the search warrant, but it was recently disclosed that the government appealed to a federal judge, G. Kendall Sharp, who granted it without explanation. The scenario played out again late last year, after prosecutors presented Magistrate Glazebrook with an application for a search warrant directed to a Sunnyvale, Calif.-based Web portal, Yahoo. The government asked that Yahoo produce web pages, documents, and usage logs pertaining to two e-mail addresses and a Web site allegedly linked to an Orlando man, Earl Beach, under investigation for involvement in child pornography. Magistrate Glazebrook allowed searches of Mr. Beach's home and computers, but again rejected prosecutors' request to acquire data located across the country. "Congress has not authorized this court to seize out-of-district property except in cases of domestic or international terrorism," the magistrate handwrote on the application. Again, prosecutors appealed. Judge Gregory Presnell took up the question and concluded that "it seems" Congress did intend to authorize nationwide search warrants in all cases, not just ones pertaining to terrorism. However, the judge acknowledged that the language Congress used was far from clear. "The court rejects the assertions made by both the United States here and the magistrate judge... that the statutory language is unambiguous. Although the court ultimately comes to a determination regarding the meaning of this language, by no means is it clearly, unambiguously or precisely written," Judge Presnell wrote. The chief federal defender in Orlando, R. Fletcher Peacock, said the dispute was a straightforward one pitting literal interpretation against legislative intent. "Judge Presnell was more willing to go behind the language of the statute and look at the statutory intent, and clearly Judge Glazebrook was not," the attorney said. One of the most striking aspects of the dispute is that there appears to be no other published court ruling addressing the nationwide-search provision, known as Section 220. The magistrate involved cited no cases directly on the point and neither did the government. An attorney with a group that pushes for online privacy, the Electronic Frontier Foundation, said yesterday that the lack of published cases on the subject reflects the fact that search warrant applications are presented outside the presence of defense lawyers, often before a defendant even knows he is under investigation. "It's fairly typical that search warrants for electronic evidence would be kept under seal," the privacy advocate, Kevin Bankston, said. "In most cases, they wouldn't be reported." Mr. Bankston said there is no question that the Justice Department wanted the Patriot Act to include nationwide-search authority for all crimes, but whether lawmakers accomplished that task is another question. "I don't know that Congress knew what it was voting on," he said. Civil libertarians have objected to the nationwide-search provision on the grounds that it allows prosecutors the discretion to pick judicial districts where judges are seen as more friendly to the government. Critics of the Patriot Act have also warned that allowing search warrants to be filed from across the country will discourage Internet service providers from fighting such requests even when they may be unwarranted. "The only person in a position to assert your rights is the ISP and if it's in their local court, they are more likely to challenge it if it is bad or somehow deficient," Mr. Bankston said. A spokesman for the prosecutors did not return a call seeking comment for this story. However, the Justice Department has said the nationwide-search provision was "vital" to its investigation of the gruesome murder in 2004 of a pregnant Missouri woman, Bobbie Jo Stinnett, whose unborn child was cut from her womb with a kitchen knife. Investigators claim that they used the Patriot Act authority to quickly obtain email evidence from an Internet provider across state lines in Kansas. That data led them to a woman who later confessed to the attack, Lisa Montgomery. In his ruling, Judge Presnell did not mention that episode, but suggested it was simpler for the courts and prosecutors to issue all warrants in a case from one place. "As a matter of judicial and prosecutorial efficiency, it is practical to permit the federal district court for the district where the federal crime allegedly occurred to oversee both the prosecution and the investigation (including the issuance of warrants) thereof," he wrote. The government has also complained that the former procedure caused court backlogs and delays in jurisdictions, like northern California, that are home to many Internet companies. It is unclear whether any charges resulted from the 2003 investigation, but the suspect involved in the disputed 2005 search, Mr. Beach, was indicted earlier this month on charges of possessing and distributing child pornography. He has pleaded not guilty. A trial is set for April. Magistrate Glazebrook said in a brief interview yesterday that he could not discuss the specific cases that prompted the legal disagreement over the Patriot Act, but that he expects the question to arise again. "It is certainly something that will come up," he said. "There are a lot of interesting issues surrounding that." |
|
Carol D. Leonnig and Mary Beth Sheridan, Washington Post
Documents cited in federal court by a defunct Islamic charity may provide the first detailed evidence of U.S. residents being spied upon by President Bush's secret eavesdropping program, according to the organization's lawsuit and a source familiar with the case.
The al-Haramain Islamic Foundation, a Saudi organization that once operated in Portland, Ore., filed a description of classified government records in a lawsuit Tuesday and immediately asked a judge for a private review. According to a source familiar with the case, the records indicate that the National Security Agency intercepted several conversations in March and April 2004 between al-Haramain's director, who was in Saudi Arabia, and two U.S. citizens in Washington who were working as lawyers for the organization. The government intercepted the conversations without court permission and in violation of the law, al-Haramain asserts in its lawsuit. It contends that eavesdropping on the conversations bypassed the Foreign Intelligence Surveillance Act, the 1978 law that requires the government to show probable cause that a U.S. resident is an agent of a terrorist group or foreign government and to obtain a warrant from the secret FISA court before monitoring that person's calls. Experts on FISA, while emphasizing that they are unfamiliar with the specifics of the al-Haramain case, said they question whether a FISA judge would agree to allow surveillance of conversations between U.S. lawyers and their client under the general circumstances described in the lawsuit. In October 2001, Bush ordered the NSA to begin monitoring some telephone calls and e-mails of U.S. residents and contacts abroad if one party was suspected to have links to terrorism. The government has said that FISA did not allow it to move quickly enough to track suspected terrorists after the Sept. 11, 2001, attacks. Several targets of government terrorism prosecutions have challenged the warrantless eavesdropping in courts nationwide since news reports in December revealed the existence of the secret surveillance program. Most of those challenges have centered on suspicion that prosecutors used information from warrantless wiretaps to build cases in terrorism investigations. This lawsuit appears to be the first to cite the government's own documents of intercepted conversations and e-mails as the reason to suspect NSA surveillance. The government has acknowledged that it targeted Iyman Faris, who pleaded guilty in 2003 to plotting to blow up the Brooklyn Bridge, for surveillance under the NSA program. Several convicted members of a group described by prosecutors as Virginia jihad network have said they believe they were targets of surveillance. The government has said it either has no evidence to support the allegation or is still investigating. Yesterday, Justice Department spokesman Brian Roehrkasse said authorities will review al-Haramain's filing. He declined to comment further. The lawsuit says that a director of al-Haramain, Suliman al-Buthe, once operated the nonprofit group in Ashland, Ore., but relocated to Saudi Arabia because of U.S. government pressure. The Treasury Department's Office of Foreign Assets Control froze the foundation's U.S. assets in February 2004, pending an investigation, and designated it a terrorist organization in September 2004, citing ties to Osama bin Laden. Al-Haramain was indicted in February 2005 on charges of conspiring to defraud the United States in connection with a scheme to funnel money to Chechen fighters. The charges were later dropped because the Oregon branch of the organization had shut down. The lawsuit contends that al-Buthe's conversations with people in the United States were illegally intercepted. In May 2004, the suit says, government officials provided al-Buthe -- apparently by accident -- copies of conversations he had with attorneys Wendell Belew and Asim Ghafoor. Later in 2004, the FBI demanded the records back, according to a source familiar with the case. Tom Nelson, an attorney for al-Haramain who filed the suit, declined yesterday to confirm the existence of any classified records or tangible evidence buttressing the suit. However, court records show, Nelson filed a motion to place material under seal as part of the suit Tuesday, and made a formal request to the judge overseeing the case to review the unspecified documents privately. |
|
Ken Livingstone
Wednesday March 1, 2006 The Guardian At least one thing can be said about my possible suspension from office, which was put on hold by the high court yesterday: people from across the political spectrum have come to the defence of the basic democratic principle that those elected by the people should only be removed by the voters.
Last week, an adjudication tribunal found that some of my comments to an Evening Standard journalist had been "unnecessarily insensitive" and "offensive". But those are not grounds for overturning the decision of the voters of London. As far as I am aware, there is no law against "unnecessary insensitivity" or even "offensiveness" to journalists questioning you as you try to go home. However, there has been an unstated allegation in this case: the implicit suggestion that my comment was anti-semitic. It is not explicitly stated because it cannot be substantiated. But the innuendo is used to give weight to charges otherwise too trivial to merit this gigantic fuss. The truth is that I have appointed black, Asian and Jewish people to the highest levels of my administration and waged an unrelenting war on every manifestation of racism, anti-semitism and every other kind of discrimination. Since I have been mayor, racial and religiously motivated incidents in the capital have declined by more than a third. Of course, there is still a problem. A Jewish person is three times more likely to suffer a racist attack than a "white European". A person of African, Caribbean or south Asian descent is 10 times more likely to suffer a racist attack. And an Arab person is 11 times more likely to suffer a racist attack in London today. But significant progress has been made against the trend that is taking place elsewhere in Europe. Associated Newspapers has always led the charge against the policies that confront racism and anti-semitism. It praised the Blackshirts in the 1930s, and admits that as recently as the retirement party of the last editor of the Daily Mail, two of its staff dressed in Nazi uniforms and were not asked to leave. The Board of Deputies, which referred me to the Standards Board, has at all times protested that this issue is just about how I treated one reporter who happens to be Jewish. I have never believed a word of it. Some time before this incident was blown up out of all proportion, the Board of Deputies asked to meet me to urge me to tone down my views on the Israeli government. For far too long the accusation of anti-semitism has been used against anyone who is critical of the policies of the Israeli government, as I have been. Even Tony Blair was recently described as a "common anti-semite" in an Israeli newspaper. Being Jewish is no defence from this charge. The famous Israeli conductor and pianist Daniel Barenboim was recently denounced by an Israeli minister as "a real Jew hater, a real anti-semite". Antony Lerman, director of the Institute for Jewish Policy Research, has said that equating criticism of Israel policies with anti-semitism "drains the word anti-semitism of any useful meaning". There is at least one positive clarification that has come out of this whole affair: Jon Benjamin, the director general of the Board of Deputies, stated last week: "We've never said the mayor is anti-semitic." The fundamental issue in this whole affair is not whether or not I was "insensitive", it is the principle that those whom the people elect should only be removed by the people or because they have broken the law. It's because this fundamental principle is at stake that I am going to do everything in my power to have this attack on the democratic rights of Londoners overturned. · Ken Livingstone is mayor of London. mayor@london.gov.uk |
|
By Charles Babington and Dan Eggen
Washington Post 1 Mar 06 Attorney General Alberto R. Gonzales appeared to suggest yesterday that the Bush administration's warrantless domestic surveillance operations may extend beyond the outlines that the president acknowledged in mid-December.
In a letter yesterday to senators in which he asked to clarify his Feb. 6 testimony to the Senate Judiciary Committee, Gonzales also seemed to imply that the administration's original legal justification for the program was not as clear-cut as he indicated three weeks ago. At that appearance, Gonzales confined his comments to the National Security Agency's warrantless wiretapping program, saying that President Bush had authorized it "and that is all that he has authorized." But in yesterday's letter, Gonzales, citing that quote, wrote: "I did not and could not address . . . any other classified intelligence activities." Using the administration's term for the recently disclosed operation, he continued, "I was confining my remarks to the Terrorist Surveillance Program as described by the President, the legality of which was the subject" of the Feb. 6 hearing. At least one constitutional scholar who testified before the committee yesterday said in an interview that Gonzales appeared to be hinting that the operation disclosed by the New York Times in mid-December is not the full extent of eavesdropping on U.S. residents conducted without court warrants. "It seems to me he is conceding that there are other NSA surveillance programs ongoing that the president hasn't told anyone about," said Bruce Fein, a government lawyer in the Nixon, Carter and Reagan administrations. A Justice Department official who spoke only on the condition of anonymity because of the sensitive nature of the program, said, however, that Gonzales's letter "should not be taken or construed to be talking about anything other than" the NSA program "as described by the president." In his letter, Gonzales revisited earlier testimony, during which he said the administration immediately viewed a congressional vote in September 2001 to authorize the use of military force against al-Qaeda as justification for the NSA surveillance program. Bush secretly began the program in October 2001, Gonzales's letter said. On Feb. 6, Gonzales testified that the Justice Department considered the use-of-force vote as a legal green light for the wiretapping "before the program actually commenced." But in yesterday's letter, he wrote, "these statements may give the misimpression that the Department's legal analysis has been static over time." Fein said the letter seems to suggest that the Justice Department actually embraced the use-of-force argument some time later, prompting Gonzales to write that the legal justification "has evolved over time." One government source who has been briefed on the issue confirmed yesterday that the administration believed from the beginning that the president had the constitutional authority to order the eavesdropping, and only more recently added the force resolution argument as a legal justification. Ranking Judiciary Committee Democrat Patrick J. Leahy (Vt.) said Gonzales's letter falls "far short of helping us focus this picture. Instead, they blur it further with vague responses about their shifting legal analysis for this illegal domestic spying and with unclear clarifications on the scope of the program over the last four years." Also yesterday, the Senate voted 69 to 30 to end a filibuster of the proposed four-year extension of the USA Patriot Act, the sweeping anti-terrorism law enacted in 2001. The Senate plans today to approve the measure, which contains hotly debated modifications. In a morning Judiciary Committee hearing, hours before Gonzales's letter was released, Fein was one of several constitutional experts who sharply challenged the constitutionality of the NSA program. Other scholars and former CIA director R. James Woolsey strongly defended it. Bush has acknowledged that he authorized the NSA to monitor phone calls and e-mails involving one party in the United States and one abroad, provided that federal agents suspect one party of terrorist ties. The administration contends that the program is not covered by the 1978 Foreign Intelligence Surveillance Act, which established a secret court to consider government requests to wiretap U.S. citizens and residents in terrorism and espionage cases. Numerous lawmakers, including Judiciary Committee Chairman Arlen Specter (R-Pa.), disagree. Specter says the NSA program violates the FISA law, and he is proposing legislation that would allow the FISA court to rule on the program's constitutionality and to oversee aspects of the surveillance operations. Woolsey, President Bill Clinton's first CIA director, defended the eavesdropping program. "The one-spy-at-a-time surveillance systems of the Cold War -- including FISA, through courts -- are not designed to deal with fast-moving battlefield electronic mapping" of today's terrorism fight, he said. "An al-Qaeda or a Hezbollah computer might be captured which contains a large number of e-mail addresses and phone numbers which would have to be checked out very promptly," he said, and the FISA warrant process is too cumbersome to allow it. © 2006 The Washington Post Company |
|
By Joe Baker, Senior Editor
The Rock River Times 1 Mar 06 Government surveillance of private individuals is more pervasive and detailed than previously thought. Investigative reporter Wayne Madsen tells us that the National Security Agency (NSA), at the center of the wiretap scandal, has expanded its surveillance of journalists that the administration claims have received classified information.
The NSA has built a database, part of the intelligence community's "Denial and Deception" operations that now holds transcripts of phone calls and e-mails among journalists and their sources and associates. The database formerly was known as "Firstfruit" until Madsen exposed it last May. Sources within the NSA told Madsen the database contains signals intelligence intercepts in violation of the Foreign Intelligence Surveillance Act (FISA), U.S. Signals Intelligence Directive 18 and the Fourth Amendment. These intercepts involve communications between certain individuals and journalists like James Bamford, James Risen, Seymour Hersh, Bill Gertz, Madsen and several others. In addition to the NSA wiretap program, it was recently revealed that the Pentagon is running its own eavesdropping operation, and there also is a top-secret wiretap program about which no information is available except a reference to it by a government employee. Along with these developments, top administration officials have pointed to the need to challenge any news they believe undercuts Bush's actions in attempting to defeat terrorists. Defense Secretary Donald Rumsfeld referred to "news informers." Add to that the announcement in January that the Army Corps of Engineers gave Halliburton subsidiary Kellogg Brown & Root a contract for $385 million to build detention centers (read concentration camps) at locations in the U.S. These centers supposedly are to deal with "an emergency influx of immigrants into the U.S., or to support the rapid development of new programs." The New York Times later reported "KBR would build the centers for the Homeland Security Department for an unexpected influx of immigrants, to house people in the event of a natural disaster or for new programs that require additional detention space." Rep. Henry Waxman, D-Calif., commented: "It's hard to believe that the administration has decided to entrust Halliburton with even more taxpayer dollars." But what might the "new programs" be? What kind of programs would call for a major expansion of detention centers, each able to hold 5,000 people? A spokesman for the Immigration and Customs Enforcement would not elaborate. Independent journalist Peter Dale Scott speculated that the "detention centers could be used to detain American citizens if the Bush administration were to declare martial law." That could include journalists and dissidents. Scott recalled that in the Reagan administration, Oliver North, then an aide to the National Security Council, organized a plan that envisioned FEMA, the Federal Emergency Management Agency, rounding up and corralling 400,000 "refugees" in the event of what he called "uncontrolled population movements" over the Mexican border into the U.S. Journalist Maureen Farrell noted that because "another terror attack is all but certain, it seems far more likely that the centers would be used for post-9/11-type detentions of immigrants rather than a sudden deluge" of immigrants flooding across the border. Daniel Ellsberg, who made public the "Pentagon Papers" in the Vietnam War era, said: "Almost certainly, this is preparation for a roundup after the next 9/11 for Mideasterners, Muslims and possibly dissenters. They've already done this on a smaller scale, with the 'special registration detentions' of immigrant men from Muslim countries, and with Guantanamo." The U.S. Army also posted a related item on its Web site. The Army posted a notice regarding the Pentagon's Civilian Inmate Labor Program. It furnishes "Army policy and guidance for setting up civilian inmate labor programs and civilian prison camps on Army installations." The timing of the posting-in the last few weeks-could be just coincidence, but the posting's reference to a "rapid action revision" and the KBR contract's expectation of "rapid development of new programs" has caused questions about the sudden need for such urgency. More attention is being focused on these developments because of earlier policies of the Bush administration to use the Pentagon in "counter-terrorism" operations inside the U.S. Even though such actions are banned by the Posse Comitatus Act, prohibiting military involvement in domestic law enforcement, the Pentagon has expanded its activities beyond previous limits, such as its part in domestic surveillance operations. Since 9/11, The Washington Post says, the Defense Department has been setting up new agencies to gather and analyze intelligence inside this country. A 2001 Defense Department memo became public in 2005. In it, the Army's top intelligence officer wrote: "Contrary to popular belief, there is no absolute ban on [military] intelligence components collecting U.S. person information." The memo made a distinction between "collecting" and "receiving" information and declared: "Military intelligence may receive information from anyone, anytime." The Pentagon also is pushing for legislation that would make an exception to the Privacy Act, which would allow the FBI and others to share citizen information with the Pentagon, CIA and other intelligence agencies. On Feb. 15, The Post reported the National Counterterrorism Center's central database contains the names of 325,000 people, said to be terrorist suspects. That's four times as many names as were in the database in the fall of 2003, and includes input from the NSA's wiretap program. |
|
By LAURIE KELLMAN
Associated Press Writer 1 Feb 06 WASHINGTON (AP) - The Senate on Wednesday agreed to add to the Patriot Act new curbs on the government's power to pry into private records, moving President Bush's antiterror law a step closer to renewal before key provisions expire next week.
But even as it progressed on a 95-4 vote, some Democrats complained that the limits would be virtually meaningless in practice and sought to add even stronger privacy protections. Majority Leader Bill Frist, R-Tenn., refused to allow more tinkering, pointing out that renewal of the 2001 law is already months overdue. The measure that passed Wednesday restricts somwhat the government's ability to access records in terrorism investigations by allowing court challenges to some demands. That's not enough for Sens. Russell Feingold, D-Wis., and Robert Byrd, D-W.Va., who were invoking several procedural maneuvers to slow down the legislation's progress. ``No one has the right to turn this body into a rubber stamp,'' said Feingold, the leading opponent of the law in Congress. ``The White House played hardball and the decision was made by some to capitulate.'' The procedural wrangling in the Senate prompted House Judiciary Committee Chairman Jim Sensenbrenner, R-Wis., to pull the measure off his chamber's schedule for the day. The House was not expected to vote on the matter until next week. Still, the law appeared headed for passage and Bush's desk before 16 major provisions were set to expire on March 10. The Senate this week is expected to pass the second measure in the two-bill package. Both have to be approved by the House before the package is sent to the White House for Bush's signature. Unable to reach accord for months, Congress has twice extended the expiration date. The 2001 anti-terrorism law was originally to have expired Dec. 31. The war on terror can't wait for more debate, Republicans said. ``Civil liberties do not mean much when you are dead,'' Sen. Jim Bunning, R-Ky., told the Senate. The Senate voted 69-30 Tuesday - 60 votes were needed - to limit debate and bring the legislation to a final vote. The Senate is expected to pass the measure as early as Wednesday, barring Democratic procedural maneuvers. The House then is expected to approve it and send the bill to Bush's desk next week. Despite the bill's progress, deep misgivings remain even among its chief supporters. One of them, Judiciary Committee Chairman Arlen Specter, R-Pa., was in the odd position Tuesday of urging his colleagues to pass a bill so flawed that he planned new legislation and hearings to fix it. ``The issue is not concluded,'' said Specter, R-Pa. He said he plans more legislation and hearings on restoring House-rejected curbs on government power. His bill would make the government satisfy a higher threshold for warrantless wiretaps and would set a four-year expiration date for the use of National Security Letters in terrorism investigations. However appetizing to Specter's colleagues in the Senate, the new bill contains items House Republicans flatly rejected during talks last year. Sensenbrenner has insisted that once the House approves the renewal and sends it to Bush, his chamber is done with the issue for the year. That will be none too soon for some lawmakers. The standoff pushed renewing the law into this midterm election year. Senate leaders were forced to find a procedural way of getting the bill to a vote without losing the support of Sensenbrenner, the Bush administration and libertarian-leaning lawmakers - all before March 10. The solution is a convoluted procedural dance that illustrates the razor-thin zone of agreement when it comes to Bush's terror-fighting law. Congress will extend the Patriot Act by passing two pieces of legislation. The first is the same accord passed last year by the House and filibustered in the Senate by members who said it contained too few privacy protections. The second is, in effect, an amendment to the first that adds enough privacy protections to win over those same libertarian-leaning Republicans. |
|
Barton Gellman, Dafna Linzer and Carol D. Leonnig, Washington Post
Intelligence officers who eavesdropped on thousands of Americans in overseas calls under authority from President Bush have dismissed nearly all of them as potential suspects after hearing nothing pertinent to a terrorist threat, according to accounts from current and former government officials and private-sector sources with knowledge of the technologies in use.
Bush has recently described the warrantless operation as "terrorist surveillance" and summed it up by declaring that "if you're talking to a member of al Qaeda, we want to know why." But officials conversant with the program said a far more common question for eavesdroppers is whether, not why, a terrorist plotter is on either end of the call. The answer, they said, is usually no. Fewer than 10 U.S. citizens or residents a year, according to an authoritative account, have aroused enough suspicion during warrantless eavesdropping to justify interception of their domestic calls, as well. That step still requires a warrant from a federal judge, for which the government must supply evidence of probable cause. The Bush administration refuses to say -- in public or in closed session of Congress -- how many Americans in the past four years have had their conversations recorded or their e-mails read by intelligence analysts without court authority. Two knowledgeable sources placed that number in the thousands; one of them, more specific, said about 5,000. The program has touched many more Americans than that. Surveillance takes place in several stages, officials said, the earliest by machine. Computer-controlled systems collect and sift basic information about hundreds of thousands of faxes, e-mails and telephone calls into and out of the United States before selecting the ones for scrutiny by human eyes and ears. Successive stages of filtering grow more intrusive as artificial intelligence systems rank voice and data traffic in order of likeliest interest to human analysts. But intelligence officers, who test the computer judgments by listening initially to brief fragments of conversation, "wash out" most of the leads within days or weeks. The scale of warrantless surveillance, and the high proportion of bystanders swept in, sheds new light on Bush's circumvention of the courts. National security lawyers, in and out of government, said the washout rate raised fresh doubts about the program's lawfulness under the Fourth Amendment, because a search cannot be judged "reasonable" if it is based on evidence that experience shows to be unreliable. Other officials said the disclosures might shift the terms of public debate, altering perceptions about the balance between privacy lost and security gained. Air Force Gen. Michael V. Hayden, the nation's second-ranking intelligence officer, acknowledged in a news briefing last month that eavesdroppers "have to go down some blind alleys to find the tips that pay off." Other officials, nearly all of whom spoke on the condition of anonymity because they are not permitted to discuss the program, said the prevalence of false leads is especially pronounced when U.S. citizens or residents are surveilled. No intelligence agency, they said, believes that "terrorist . . . operatives inside our country," as Bush described the surveillance targets, number anywhere near the thousands who have been subject to eavesdropping. The Bush administration declined to address the washout rate or answer any other question for this article about the policies and operations of its warrantless eavesdropping. Vice President Cheney has made the administration's strongest claim about the program's intelligence value, telling CNN in December that eavesdropping without warrants "has saved thousands of lives." Asked about that Thursday, Hayden told senators he "cannot personally estimate" such a figure but that the program supplied information "that would not otherwise have been available." FBI Director Robert S. Mueller III said at the same hearing that the information helped identify "individuals who were providing material support to terrorists." Supporters speaking unofficially said the program is designed to warn of unexpected threats, and they argued that success cannot be measured by the number of suspects it confirms. Even unwitting Americans, they said, can take part in communications -- arranging a car rental, for example, without knowing its purpose -- that supply "indications and warnings" of an attack. Contributors to the technology said it is a triumph for artificial intelligence if a fraction of 1 percent of the computer-flagged conversations guide human analysts to meaningful leads. Those arguments point to a conflict between the program's operational aims and the legal and political limits described by the president and his advisers. For purposes of threat detection, officials said, the analysis of a telephone call is indifferent to whether an American is on the line. Since Sept. 11, 2001, a former CIA official said, "there is a lot of discussion" among analysts "that we shouldn't be dividing Americans and foreigners, but terrorists and non-terrorists." But under the Constitution, and in the Bush administration's portrait of its warrantless eavesdropping, the distinction is fundamental. Valuable information remains valuable even if it comes from one in a thousand intercepts. But government officials and lawyers said the ratio of success to failure matters greatly when eavesdropping subjects are Americans or U.S. visitors with constitutional protection. The minimum legal definition of probable cause, said a government official who has studied the program closely, is that evidence used to support eavesdropping ought to turn out to be "right for one out of every two guys at least." Those who devised the surveillance plan, the official said, "knew they could never meet that standard -- that's why they didn't go through" the court that supervises the Foreign Intelligence Surveillance Act, or FISA. Michael J. Woods, who was chief of the FBI's national security law unit until 2002, said in an e-mail interview that even using the lesser standard of a "reasonable basis" requires evidence "that would lead a prudent, appropriately experienced person" to believe the American is a terrorist agent. If a factor returned "a large number of false positives, I would have to conclude that the factor is not a sufficiently reliable indicator and thus would carry less (or no) weight." Bush has said his program covers only overseas calls to or from the United States and stated categorically that "we will not listen inside this country" without a warrant. Hayden said the government goes to the intelligence court when an eavesdropping subject becomes important enough to "drill down," as he put it, "to the degree that we need all communications." Yet a special channel set up for just that purpose four years ago has gone largely unused, according to an authoritative account. Since early 2002, when the presiding judge of the federal intelligence court first learned of Bush's program, he agreed to a system in which prosecutors may apply for a domestic warrant after warrantless eavesdropping on the same person's overseas communications. The annual number of such applications, a source said, has been in the single digits. Many features of the surveillance program remain unknown, including what becomes of the non-threatening U.S. e-mails and conversations that the NSA intercepts. Participants, according to a national security lawyer who represents one of them privately, are growing "uncomfortable with the mountain of data they have now begun to accumulate." Spokesmen for the Bush administration declined to say whether any are discarded. New Imperatives Recent interviews have described the program's origins after Sept. 11 in what Hayden has called a three-way collision of "operational, technical and legal imperatives." Intelligence agencies had an urgent mission to find hidden plotters before they could strike again. About the same time, advances in technology -- involving acoustic engineering, statistical theory and efficient use of computing power to apply them -- offered new hope of plucking valuable messages from the vast flow of global voice and data traffic. And rapidly changing commercial trends, which had worked against the NSA in the 1990s as traffic shifted from satellites to fiber-optic cable, now presented the eavesdroppers with a gift. Market forces were steering as much as a third of global communications traffic on routes that passed through the United States. The Bush administration had incentive and capabilities for a new kind of espionage, but 23 years of law and White House policy stood in the way. FISA, passed in 1978, was ambiguous about some of the president's plans, according to current and retired government national security lawyers. But other features of the eavesdropping program fell outside its boundaries. One thing the NSA wanted was access to the growing fraction of global telecommunications that passed through junctions on U.S. territory. According to former senator Bob Graham (D-Fla.), who chaired the Intelligence Committee at the time, briefers told him in Cheney's office in October 2002 that Bush had authorized the agency to tap into those junctions. That decision, Graham said in an interview first reported in The Washington Post on Dec. 18, allowed the NSA to intercept "conversations that . . . went through a transit facility inside the United States." According to surveys by TeleGeography Inc., nearly all voice and data traffic to and from the United States now travels by fiber-optic cable. About one-third of that volume is in transit from one foreign country to another, traversing U.S. networks along its route. The traffic passes through cable landing stations, where undersea communications lines meet the East and West coasts; warehouse-size gateways where competing international carriers join their networks; and major Internet hubs known as metropolitan area ethernets. Until Bush secretly changed the rules, the government could not tap into access points on U.S. soil without a warrant to collect the "contents" of any communication "to or from a person in the United States." But the FISA law was silent on calls and e-mails that began and ended abroad. Even for U.S. communications, the law was less than clear about whether the NSA could harvest information about that communication that was not part of its "contents." "It's the nature of intelligence that many tips lead nowhere, but you have to go down some blind alleys to find the tips that pay off." -- Air Force Gen. Michael V. Hayden on Jan. 23. (By Lauren Victoria Burke -- Associated Press) "We debated a lot of issues involving the 'metadata,' " one government lawyer said. Valuable for analyzing calling patterns, the metadata for telephone calls identify their origin, destination, duration and time. E-mail headers carry much the same information, along with the numeric address of each network switch through which a message has passed. Intelligence lawyers said FISA plainly requires a warrant if the government wants real-time access to that information for any one person at a time. But the FISA court, as some lawyers saw it, had no explicit jurisdiction over wholesale collection of records that do not include the content of communications. One high-ranking intelligence official who argued for a more cautious approach said he found himself pushed aside. Awkward silences began to intrude on meetings that discussed the evolving rules. "I became aware at some point of things I was not being told about," the intelligence official said. 'Subtly Softer Trigger' Hayden has described a "subtly softer trigger" for eavesdropping, based on a powerful "line of logic," but no Bush administration official has acknowledged explicitly that automated filters play a role in selecting American targets. But Sen. Arlen Specter (R-Pa.), who chairs the Judiciary Committee, referred in a recent letter to "mechanical surveillance" that is taking place before U.S. citizens and residents are "subject to human surveillance." Machine selection would be simple if the typical U.S. eavesdropping subject took part in direct calls to or from the "phone numbers of known al Qaeda" terrorists, the only criterion Bush has mentioned. That is unusual. The NSA more commonly looks for less-obvious clues in the "terabytes of speech, text, and image data" that its global operations collect each day, according to an unclassified report by the National Science Foundation soliciting research on behalf of U.S. intelligence. NSA Inspector General Joel F. Brenner said in 2004 that the agency's intelligence officers have no choice but to rely on "electronic filtering, sorting and dissemination systems of amazing sophistication but that are imperfect." One method in use, the NSF report said, is "link analysis." It takes an established starting point -- such as a terrorist just captured or killed -- and looks for associated people, places, things and events. Those links can be far more tenuous than they initially appear. In an unclassified report for the Pentagon's since-abandoned Total Information Awareness program, consultant Mary DeRosa showed how "degrees of separation" among the Sept. 11 conspirators concealed the significance of clues that linked them. Khalid Almihdhar, one of the hijackers, was on a government watch list for terrorists and thus a known suspect. Mohamed Atta, another hijacker, was linked to Almihdhar by one degree of separation because he used the same contact address when booking his flight. Wail M. Alshehri, another hijacker, was linked by two degrees of separation because he shared a telephone number with Atta. Satam M.A. Al Suqami, still another hijacker, shared a post office box with Alshehri and, therefore, had three degrees of separation from the original suspect. Those links were not obvious before the identity of the hijackers became known. A major problem for analysts is that a given suspect may have hundreds of links to others with one degree of separation, including high school classmates and former neighbors in a high-rise building who never knew his name. Most people are linked to thousands or tens of thousands of people by two degrees of separation, and hundreds of thousands or millions by three degrees. Published government reports say the NSA and other data miners use mathematical techniques to form hypotheses about which of the countless theoretical ties are likeliest to represent a real-world relationship. A more fundamental problem, according to a high-ranking former official with firsthand knowledge, is that "the number of identifiable terrorist entities is decreasing." There are fewer starting points, he said, for link analysis. "At that point, your only recourse is to look for patterns," the official said. Pattern analysis, also described in the NSF and DeRosa reports, does not depend on ties to a known suspect. It begins with places terrorists go, such as the Pakistani province of Waziristan, and things they do, such as using disposable cell phones and changing them frequently, which U.S. officials have publicly cited as a challenge for counterterrorism. "These people don't want to be on the phone too long," said Russell Tice, a former NSA analyst, offering another example. Analysts build a model of hypothetical terrorist behavior, and computers look for people who fit the model. Among the drawbacks of this method is that nearly all its selection criteria are innocent on their own. There is little precedent, lawyers said, for using such a model as probable cause to get a court-issued warrant for electronic surveillance. Jeff Jonas, now chief scientist at IBM Entity Analytics, invented a data-mining technology used widely in the private sector and by the government. He sympathizes, he said, with an analyst facing an unknown threat who gathers enormous volumes of data "and says, 'There must be a secret in there.' " But pattern matching, he argued, will not find it. Techniques that "look at people's behavior to predict terrorist intent," he said, "are so far from reaching the level of accuracy that's necessary that I see them as nothing but civil liberty infringement engines." 'A Lot Better Than Chance' Even with 38,000 employees, the NSA is incapable of translating, transcribing and analyzing more than a fraction of the conversations it intercepts. For years, including in public testimony by Hayden, the agency has acknowledged use of automated equipment to analyze the contents and guide analysts to the most important ones. According to one knowledgeable source, the warrantless program also uses those methods. That is significant to the public debate because this kind of filtering intrudes into content, and machines "listen" to more Americans than humans do. NSA rules since the late 1970s, when machine filtering was far less capable, have said "acquisition" of content does not take place until a conversation is intercepted and processed "into an intelligible form intended for human inspection." The agency's filters are capable of comparing spoken language to a "dictionary" of key words, but Roger W. Cressey, a senior White House counterterrorism official until late 2002, said terrorists and other surveillance subjects make frequent changes in their code words. He said, " 'Wedding' was martyrdom day and the 'bride' and 'groom' were the martyrs." But al Qaeda has stopped using those codes. An alternative approach, in which a knowledgeable source said the NSA's work parallels academic and commercial counterparts, relies on "decomposing an audio signal" to find qualities useful to pattern analysis. Among the fields involved are acoustic engineering, behavioral psychology and computational linguistics. A published report for the Defense Advanced Research Projects Agency said machines can easily determine the sex, approximate age and social class of a speaker. They are also learning to look for clues to deceptive intent in the words and "paralinguistic" features of a conversation, such as pitch, tone, cadence and latency. This kind of analysis can predict with results "a hell of a lot better than chance" the likelihood that the speakers are trying to conceal their true meaning, according to James W. Pennebaker, who chairs the psychology department at the University of Texas at Austin. "Frankly, we'll probably be wrong 99 percent of the time," he said, "but 1 percent is far better than 1 in 100 million times if you were just guessing at random. And this is where the culture has to make some decisions." |
|
DemocracyNow
1 Mar 06 We speak with Liz McIntyre, author of "Spychips: How Major Corporations and Government Plan to Track your Every Move with RFID" that examines radio frequency identification - a technology that uses tiny computer chips to track items at distance. Major corporations are working right now to install RFIDs on all consumer products.
Imagine a world of no more privacy. "Where your every purchase is monitored and recorded in a database, and your every belonging is numbered. Where someone many states away or perhaps in another country has a record of everything you have ever bought, of everything you have ever owned, of every item of clothing in your closet -- every pair of shoes. What's more, these items can even be tracked remotely. "Once your every possession is recorded in a database and can be tracked, you can also be tracked and monitored remotely through the things you wear, carry and interact with every day. "We may be standing on the brink of that terrifying world if global corporations and government agencies have their way. It's the world that Wal-Mart, Target, Gillette, Procter & Gamble, Kraft, IBM, and even the United States Postal Service want to usher in within the next ten years. "It's the world of radio frequency identification. "Radio frequency identification, RFID for short, is a technology that uses tiny computer chips -- some smaller than a grain of sand -- to track items at distance. If the master planners have their way, every object -- from shoes to cars -- will carry one of these tiny computer chips that can be used to spy on you without your knowledge or consent." Those are the opening words of the book, "Spychips: How Major Corporations and Government Plan to Track your Every Move with RFID." Today we are joined by one of the co-authors of "Spychips" - Liz McIntyre. * Liz McIntyre, a consumer privacy expert and author of "Spychips: How Major Corporations and Government Plan to Track your Every Move with RFID." She serves as the Communications Director for CASPIAN (Consumers Against Supermarket Privacy Invasion and Numbering), a grass-roots organization that has been tackling consumer privacy issues since 1999. She also writes about consumer issues as the MoneyMom, a syndicated family money writer and columnist. - Website: Spychips.com * Annalee Newitz, freelance journalist. She writes about the intersection of technology science and culture and is a contributing editor at Wired Magazine. She recently had an RFID implanted in her arm. - Website: Techsploitation.com Listen to Segment || Download Show mp3 Watch 128k stream Watch 256k stream To purchase an audio or video copy of this entire program, click here for new online ordering or call 1 (888) 999-3877. |
|
By Amy Worthington
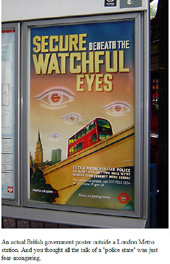
Idaho Observer 1 Mar 06 Senate Minority leader Harry Reid (D-NV) calls this Congress the "most corrupt" in history.1 U.S. Representative Ron Paul (R-TX) often uses the term "police state" to describe our national state of affairs. George Bush is making the most expansive claims to unbridled power since America's War for Independence, according to Senator Patrick Leahy (D-VT).2 Former U.S. Ambassador Joseph Wilson, who proved Bush lied to launch us into war with Iraq, says "fascist forces have seized control of the levers of power."3 Americans are being told that their Republic has become a fascist police state-they just need ears to hear.
In a fascist police state, the dictator secures his power with support from private corporations which are given special privileges and, thus, benefit from doing business with dictators. Continuously bribed by 28,000 corporate lobbyists in D.C.,4 Congress is doing its part to build a fascist state in America. During President Bush's recent State of the Union speech, these tainted legislators perpetually rose to their feet to applaud the spewing of what a New York Times editorial called "misleading analogies, propaganda slogans and false choices."5 Their bootlicking recalls a by-gone Soviet era when endless rows of robotic Central Party members applauded the likes of Stalin to ensure their next breath of oxygen. Passing the fascist laws they never read After passage of the Patriot Act of 2001, Rep. Paul told Insight Magazine that the 2,200-page bill was not made available to Congress to read before the vote.6 So the most corrupt Congress in history rubber stamped the most fascist legislation they had never read. Our constitution enumerates inalienable rights that are emphatically restated in the first 10 amendments commonly known as "The Bill of Rights." Under the Patriot Act, the "right" to free speech, peaceable assembly and security in one's person, papers and effects have been relegated to "privileges" that government can take away at any time. Patriot Act authority has suspended the right to due process and a prompt and public trial; it even cancelled protection against cruel and unusual punishment. Agents serving the fascist state can freely wire-tap our phones, enter our homes/offices, search and seize without warrant and detain us indefinitely without charges-ostensibly to keep America safe. As we go to press, the original Patriot Act, which had a sunset clause, is now in the final stages of being amended and passed by Congress as a permanent feature of America's fascist landscape. The ink had barely dried on the Patriot Act when Congress passed the Homeland Security Act of 2002. Rep. Paul stated that Congress also did not read the 500-page bill that gave birth to the Department of Homeland Security (DHS).7 DHS, a creepy intelligence gathering apparatus reminiscent of the Nazi SS, has merged 22 federal agencies and their databases, employing nearly a quarter million workers. The New York Times columnist William Safire told the American people that, under DHS, "You are a suspect."8 Rep. Paul confirms that "the Department represents a huge new increase in the size and scope of the federal government that will mostly serve to spy on the American people."9 Fascist-to the bones Michael Chertoff was appointed by Bush in 2004 to head DHS. Chertoff appears to be an identical twin of founding Soviet dictator Vladimir Lenin, giving us a stark flashback to the Russian Revolution of 1917. That lucrative Wall Street operation, which unleashed murderous communist tyranny upon hundreds of millions of people for nearly the entire 20thcentury, was funded and directed from New York by a clique of Yale-graduated Skull and Bones members in business with the Averell Harriman family.10 George Herbert Walker, great grandfather of the Skull and Bones fascist now occupying the White House, was a Harriman partner when Lenin granted to Harriman's Wall Street syndicate lucrative Russian resource concessions.11 Lenin also made Harriman partner Max May of Wall Street's Guaranty Trust the first vice president of Russia's Soviet Ruskombank.12 Yale's powerful Skull and Bones network also has a predilection for fascism, as clearly illustrated by the Harriman-Bush involvement in secret funding of the German Nazis during the 1930s.13 Our present commander-in-chief's grandfather, Prescott Sheldon Bush, was a Harriman partner involved in business dealings with Hitler's war machine even after WWII began.14 Prescott shamelessly failed to divest himself of more than a dozen "enemy national" relationships that continued as late as 1951.15 As we witness the progression of runaway fascism under the administration of Prescott's grandson, we must recall that the Skull and Bones syndicate, so adept at bringing nations to heel with war and revolution, created the CIA in 1947 under direction of Bonesman Robert A. Lovett.16 Our burgeoning fascist state is a raging metastasis of the syndicate's obsession with power, made possible by it's ritualistic secrecy and iron-fisted control of U.S. intelligence for the last 60 years. Our present generation of ruling Bonesmen is now brazenly merging the hideous Soviet and Nazi models into a hybrid for the new U.S. Homeland Security state. Congress reforms "intelligence" In 2004, a clueless and/or compromised Congress rubber-stamped the Intelligence Reform Act, a bill weighing in at over 3,000 pages. This Orwellian horror created the Department of National Intelligence (DNI). All 15 U.S. intelligence agencies now report to DNI mega-commissar John Negroponte, a veteran of the Iran-Contra scandal. This shady new law also establishes a counter-terrorism center and provides for a spy satellite network capable of monitoring private communications systems. It mandates that all drivers licenses and birth certificates be standardized, thereby creating a national ID system. Some provisions of the Intelligence Reform Act were classified "top secret" and congressmen were not allowed to read them.17 Americans have yet to discover what malignant ramifications the DNI may hold for the future. In June, 2005, George Bush placed a portion of the FBI under his personal control, creating the National Security Service. This secret police apparatus, to be operated by the White House, will have no congressional oversight.18 In October, 2005, Bush created by executive order the National Clandestine Service, a new sticky arm of the CIA empowered to carry out covert operations, spying and dirty tricks within the United States.19 How many Gestapo units does a Fuhrer need? Meantime, we saw the true fascist face of Chertoff's Homeland Security megalith last year when he called together some 50 big corporations, including Microsoft, Oracle and Verizon, to enlist their help in watching and tracking the activities of Americans. He told them that Homeland Security was considering hiring a non-profit group to gather information on citizens and send their names for scrutiny to Homeland Security.20 This is the classic fascist formula-corporations invited by Homeland Security to enrich themselves by keeping 300 million Americans under surveillance as suspicious characters. The Department is now collecting a gargantuan amount of information, on every citizen-from every imaginable source- with its new "dataveillance" system called "Analysis, Dissemination, Visualization, Insight and Semantic Enhancement (ADVISE)." By sifting through mountains of computerized information, Chertoff's Gestapo may now identify our "critical patterns of behavior" in order to assess our "motives and intentions."21 An extremely paranoid surveillance state emerges Homeland Security is grooming law enforcement agencies across the nation to keep a suspicious eye on everyone. A 2004 Homeland Security memo22 sent to police departments and sheriffs' offices all over the nation instructed law enforcement personnel to watch the masses for body language since a scratch here, a twitch there could give away a would-be terrorist attempting to blend into everyday American life while planning an attack. The memo warned of anyone who shows arrogance or expresses "dislike of attitudes and decisions of the U.S. government," implying that dissent is synonymous with terrorism and to consider as suspect an emotionless face or "a pale face from the recent shaving of a beard." It also warned that a terrorist might find waiting in a grocery store line intolerable. So we learn that to prevent suspicion, good Homeland citizens must refrain from twitching or scratching in public and maintain a happy face at the grocery store. The Washington Post noted that each of the U.S. military branches is also spying domestically on American citizens. This has been confirmed by Senator Ron Wyden (D-OR), a member of the Senate Select Committee on Intelligence who was outraged when he told The Washington Post last November, "We are deputizing the military to spy on law-abiding Americans in America."23 One tentacle of this domestic military spy apparatus is the Pentagon's Counterintelligence Field Activity (CIFA), a conglomeration of powerful directorates which collect and analyze names of persons considered a threat to the infrastructure of the fascist state.24 Professor of politics Christopher Pyle explains that the Joint Terrorism Task Forces (JTTF) unite military analysts with law enforcement agents as part of "one big club effectively destroying the Fourth Amendment against unlimited search and seizure."25 Commentator Steve Weissman confirms that the JTTF, FBI and local cops are quietly building their own ad-hoc secret police.26 The Pentagon-with its huge network of intelligence agencies-is reportedly engaged in a power struggle with Congress and the new DNI. Defense Secretary Rumsfeld is infamous for trying to make his own foreign policy. 27 He has created a new intelligence apparatus of his very own, the Strategic Support Branch (SSB). According to The New York Times, Rumsfeld's SSB networks, now deployed in nations across the globe, are immune from both congressional oversight and media examination.28 Special operations teams now roam the planet to perpetrate Rumsfeld's personal black ops missions with no records kept and no questions asked.29 Some of these operations are headed up by Lt. General William Boykin30 who calls the U.S. Army the "House of God"-war, militarism and coercive surveillance being a sort of fascist religion, you see. The Pentagon also controls the National Security Agency which was authorized by Bush, in violation of the law, to conduct illegal and warrantless wire-tapping of American citizens before 9/11. About the minute he seized the White House, Bush directed NSA to launch a frenetic illegal domestic spy program, depriving Americans of their Fourth Amendment protection from unjustified government intrusion.31 That was long before he could use the excuse of terrorism. To his credit, Senator Russ Feingold said he felt shame during the 2006 State of the Union speech when his fellow legislators wildly applauded as Bush defended this illegal surveillance. "Since when do we start to stand up and cheer for breaking the law?" Feingold asked.32 The New York Times reported that after 9/11, NSA went hysterical, sending the names, addresses and emails of thousands Americans to the FBI for investigation.33 In Idaho (and throughout the nation), law abiding Muslims were harassed and questioned incessantly by the FBI. Finally the ACLU held a seminar to teach these people how to defend themselves during endless interrogations.34 The FBI was overwhelmed with NSA demands-yet we now know that the FBI located no terrorist cells inside the U.S.35 and managed mainly to terrify innocent citizens and invade their privacy.36 The government and its contractors shall be held blameless Additional police state spawn known as the "Project Bioshield Act of 2004," authorizes the secretaries of the DHS and the Department of Health and Human Services (DHHS) to take virtual control of the bodies of all American citizens during a national emergency. Health officials are empowered to compel everyone to receive state-mandated medications or vaccinations and to comply with quarantine orders.37 With lavish Project Bioshield funding, state and local agencies have been drilling for the day when citizens are commanded to line up for the bio-terrorism counter measures being brewed for them by large pharmaceutical companies under lucrative federal contracts. Absolute liability protection for those companies was inserted into The Public Readiness and Emergency Preparedness Act passed in December, 2005. According to outraged congressional witnesses, Senate Majority Leader Bill Frist and House speaker Dennis Hastert used devious chicanery to sneak this provision into the language without approval of the House-Senate conference committee responsible for the final draft.38 Now if citizens are sickened or killed by Homeland's compulsory bio-warfare drugs and vaccines, they can neither sue the manufacturer nor seek compensation from the government. This safety net for the pharmas is vital because the new recombinant vaccines contain deadly squalene adjuvants like MF59, or other lipid-based additives like MPL. These non-soluble lipids cause extreme inflammation as they gradually go rancid in the body. Test animals injected with lipid-based adjuvants always develop incurable auto-immune conditions symptomatic of multiple sclerosis, rheumatoid arthritis and systemic lupus.39 Hundreds of military personnel injected with experimental lots of squalene-contaminated anthrax vaccines have also developed painful, incurable chronic illnesses.40 When Homeland needle Nazis start forcibly whacking the population with the new lipid-laced vaccines, Americans will truly understand the meaning of "bioterrorism." The new limits of imagination Meantime, as Homeland fascism deeply ripens, reports of Gestapo-like surveillance and intrusions are coming from everywhere. Doug Thompson, a longtime D.C. reporter with deep connections-whose website Capitol Hill Blue has kept readers apprised of the increasingly bizarre and erratic behavior of George W. Bush-recently discovered that the FBI has collected over 100 pages of trivial information on him since 9/11. A friend in the Justice Department actually showed him the data.41 Another award-winning news correspondent James Moore, who co-authored a book critical of Bush, went to the airport to catch his reserved flight and was told he is now on the Transportation Security Administration's no-fly list. He has never been given a reason why. If you anger the dictator in a police state, you have no rights. Moore has no recourse; no appeal.42 Homeland Security is now freely opening private mail.43 Internet providers, universities and city governments across the nation are being forced to overhaul their internet computer networks to make it easier for law enforcement to monitor on-line communications.44 Companies like Yahoo and Google have been pressured to turn over their databases so snoopers can see what websites Americans are visiting.45 The Washington Post informs us that the FBI is still hand-delivering thousands of national security letters to banks, libraries and commercial enterprises across the nation demanding they turn over their records on their patrons, thus allowing inquisitors to secretly learn every intimate detail of our finances.46 Anti-war protestors across the nation report that they are being watched and harassed by the National Security Agency and by certain National Guard and local police units working with federal agencies.47 The most outrageous report is that of a young high school student in North Carolina given an assignment to illustrate his rights under the Bill of Rights. He took a photo of a George Bush poster hanging on the wall next to a "thumbs down" sign. A Walmart employee freaked when he developed the photo and called the police, who then called the Secret Service. The Secret Service went ballistic. They grilled the principal and the civics teacher, confiscated the photo poster and threatened to indict the terrified student.48 Now this kid truly understands the new Bill of no Rights in Fascist America. And the fantasmagorical horse it rode in on Especially galling is that all of this lunacy has blossomed since the so-called terrorist attack of 9/11. As millions of Americans now know-the official 9/11 fable violates the laws of natural science. A jet liner can't disappear into a hole less than half its size without leaving wreckage (Pentagon). Hijackers can't be killed in plane crashes and later be found alive and living lawfully in various locations throughout the world. Smoldering fires too cool to bend, let alone melt steel girders can't collapse two skyscrapers simultaneously at the speed of gravity (Twin Towers). Brigham Young University physics professor Steven Jones has demonstrated mathematically that pre-positioned explosives, detonated in precise sequence, brought the Trade Center buildings down.49 Former German Minister Andreas Von Beulow has explained to the entire world why the complex 9/11 attack was impossible without U.S. government and corporate backing.50 Russian General Leonid Ivashov said recently that the 9/11 attack was faked by government and corporate officials who have invented the war on terror as a tool for global political and economic manipulation.51 Hundreds of 9/11 families know this and in May 2002, they filed suit against the feds for the sacrificial death of their loved ones.52 Their attorney, Stanley Hilton, has stated that he went to school years ago with Paul Wolfowitz and other Bush advisors who even then were planning a fake Pearl Harbor-like attack to grease the skids for a presidential dictatorship.53 Because these sociopaths got away with 9/11, the door remains wide open for them to unleash future fake attacks to leap frog their fascist plans forward. Keeping a corrupt Congress in tow The most corrupt Congress in history has collaborated with 9/11 perpetrators in a shameful cover-up of this horrible genocide project. Perhaps they tolerate treason because they are afraid to end up like the late Senator Paul Wellstone, who died in a suspicious plane crash after leading opposition to the Bush gang's war in Iraq.54 Or they are afraid of getting an anthrax message as did the staffs of Tom Daschle and Pat Leahy after those two sassed the president back in 2001.55 According to research of Dr. Len Horowitz and others, the anthrax strain mailed to enemies of the state originated in a CIA research program. It is apparent that even the anthrax scare was an inside job.56 If America gets the flu, will it be from "the birds"-or from "the boys?" Waive Posse Comitatus; suspend habeas corpus In October 2005, Bush announced that he was considering plans for federal military personnel to enforce quarantines in the event of a bird flu outbreak. Bush believes that he has the power to waive the 1878 Posse Comitatus Act, which prohibits federal military personnel from committing law enforcement in the United States. John Brinkerhoff, deputy director of FEMA, has developed martial law implementation plans to be enforced by U.S military personnel. Bush has reportedly signed executive orders giving himself sole authority to impose martial law and suspend habeas corpus with no checks and balances during a national emergency.57 When implemented, the declaration of martial law will completely trump the sovereign powers of the several states. In his hands? The authority to decide what constitutes a national emergency apparently rests solely with this impaired little man who needs antidepressants to control his moods and temper.58 Our cherished Constitution now dangles by a thread from the unstable hand of a man professionally diagnosed as a paranoid meglomanic.59 The lives of our children now depend upon a man who has authorized the Pentagon's use of flesh burning white phosphrous and napalm weapons against the people of Iraq in the name of bringing them "democracy."60 The Pentagon has ordered U.S. Northern Command (NORTHCOM) at Peterson Air Force Base to prepare a series of CONPLANS, super secret strategies designed for rapid military takeover of the USA when the dictator gives the word.61 These are the same planners who, under the command of Defense Secretary Donald Rumsfeld were, "unable" to get a single plane off the ground to intercept the attack they launched against their own headquarters to engender the fascism we now suffer. 62 William Arkin, writing for The Washington Post, explains that the CONPLANS have arisen from a series of special authorities given to the Pentagon by the White House. The Pentagon's full scale exercise of CONPLAN 0400 (Granite Shadow) capabilities are slated to begin in April 2006.63 A preview was seen when fully armed Visible Intermodal Protection and Response (VIPER) teams launched exercises in U.S. mass transit facilities late last year. As noted by writer Steve Watson, VIPER exercises involved "federally brainwashed goons stomping around with machine guns and vicious dogs, getting in everyone's face and randomly grabbing and searching people on the subway."64 General Tommy Franks assured us in 2003 that, after a major casualty-producing event anywhere in the Western world, the American people would "question our own constitution" and consent to a militarization of the United States for security.65 The Pentagon is said to be a tad worried that a military takeover at home might diminish its ability to kill and torture abroad.66 The fascists and their friends are preparing for martial law Halliburton subsidiary Kellogg, Brown and Root has been awarded a $385 million dollar contract by Homeland Security for construction of detention and processing facilities to be made ready in the event of a national emergency.67 Brown and Root has been part of the Skull and Bones nexus since its inception at the turn of last century.68 Like Halliburton, it has grown fat on blood-money gleaned through decades of perpetual war, including the present conflagration in the Middle East. If the fascists batten down totalitarian power domestically, Kellogg, Brown and Root will likely profit immensely from the erection and maintenance of such prison camps expected to dot the land of the free if the fascists launch a military takeover. Homeland Security camps could be bulging at the seams overnight when the U.S. falls under "emergency" military rule. Indeed, the foregoing shows the Bush administration is preparing for this eventuality. The U.S. already has the highest per capita incarceration rate in the world. During martial law, when no one is free to move around at will, just about EVERYONE is under a form of "house" arrest. Americans got a taste of this grim future when, during the 2004 Republican National Convention protests when 1,806 demonstrators were rounded up, imprisoned without charges and kept in filthy conditions for 24 hours or more.69 New national ID: A totalitarian dream coming true The grand finale of American fascism is yet to come. No totalitarian ruling structure would be complete without an oppressive identification system that allows the dictator's henchmen to access birth-to-death information on every citizen listed in the national database. It's becoming obvious that no one is intended to escape the dictator's dynamic plans to force upon us national ID cards and, eventually, under-the-skin identification implants and a satellite tracking system able to keep each of us under round-the-clock surveillance. The CIA admits that for years it has supported the rise of numerous U.S. technology companies for the development of hardware and software useful for surveillance and tracking of the masses.70 Oracle Corporation, the world's largest database software maker, is one of these CIA receptacles.71 As a voice for spooks everywhere, Oracle's billionaire chairman Larry Ellison has long demanded that Americans be encumbered with digital identification cards, complete with biometric markers such hand prints and iris scans.72 Immediately after 9/11, Ellison presented to federal officials his proposal to create a national ID system with Oracle's expertise and technology. This system will provide ruling fascists with utmost efficiency at sucking detailed personal information on every citizen into what Ellison calls a "single comprehensive national security file."73 The U.S. Intelligence Reform Bill of 2004 made a portion of Ellison's proposal into law. It requires that each new U.S. citizen born be issued a Social Security number to be included on his birth certificate along with his DNA biomarkers. All of this information will be stored in the national data base and no child will enroll in public school or receive any entitlement benefit without first presenting his Homeland Security birth certificate.74 The Real ID Act passed by Congress in December 2005 completely solidified Ellison's ID plan. This new law establishes a massive, centrally-coordinated federal ID database. It forces all 50 states to spend millions of dollars to update their equipment so that by 2008, all holders of U.S. drivers licenses and state licensed ID cards will have their biometric data and other personal information fed directly into the national data base. Congressman Paul says the new ID cards will likely contain radio frequency identification tracking technology that can be read by scanners at a distance, allowing the governments of U.S., Canada and Mexico to quickly locate any card-bearing American.75 We are told that banks and credit card companies applaud a national ID system.76 Instead of using bank credit and debit cards, people may eventually make purchases by showing their biometric Homeland ID cards. These transactions will then end up in the federal database, permitting fascists to assess our motives and intentions by monitoring our cashless sales and purchases. Officials at all levels will also be able to feed a citizen ID number into a wireless handheld or laptop device that connects to the national database. They may then instantly access that person's financial transactions, credit reports, medical and vaccination records, school records, driving records, political and religious affiliations and anything else that might have been inserted into his file by Homeland spies. If this were 2008, the boy who created the thumbs down poster would likely have his politically incorrect behavior duly recorded in the national data base under his ID number. And conversely, while Americans are being set up to surrender every shard of personal privacy, their fascist government is withholding from them more information than ever and continually expanding ways of shrouding data, according to a coalition of watchdog groups.77 Can you say "Mooo, baa baa" and "oink?" National ID cards are only the beginning. America's fascist police state is demonstrably anxious to ensure that each citizen have his identification number permanently attached to his body. For many years, U.S. intelligence agencies have been working with private corporations and covens of scientists from Princeton University and other enclaves to develop subdermal radio frequency devices that can be injected under the skin of humans for identification purposes. Syringe implantable ID transponders were readied years ago, as illustrated by the prototype fully developed in 1995 by CIA-connected Hughes Aircraft Company.78 The corporate gargoyle chosen by the fascists to market ID implant devices for our new security state is Applied Digital Solutions (ADS). With corporate offices in Florida, ADS and its web of subsidiaries are now unleashing upon the world a vast variety of injectable ID chips, plus the sensors and scanners needed to read them.79 A leading ADS backer is IBM, which promotes a global identity system.80 It's a matter of public record that IBM's New York Office provided the German Nazi's with technology and equipment that allowed Hitler to number and track his Nazi concentration camp prisoners as well as others caught in his fascist web.81 If he could he see his old partners now, Adolph might be green with envy, having been consigned to the barbaric practice of simply tattooing ID numbers on his slaves. While many European nations are also setting up electronic identity systems as a foundation for future ID chip implants, it is especially pertinent that ADS has been given a prestigious award for its sinister implant technology by the World Economic Forum (WEF).82 WEF is a clique of wealthy corporate and political elitists who dictate global agendas. One of its most famous members is Bill Gates of Microsoft. Gates travels the world spending millions to promote injections for people of Third World nations. ID microchip implants are the mother of all injections. Microsoft recently patented a way to use human skin as a power conduit for electronic devices.83 Chipping away In 2004, Tommy Thompson, at that time the Secretary of Health and Human Services under Homeland Security, invited ADS to a government showcase to promote the implantation of subdermal microchips as part of the U.S. health care system.84 Requiring no medical control studies on the health effects of microchip implantation, the FDA, which also gave us silicone breast implants, aspartame and Vioxx, has approved the marketing of certain ADS chips.85 Tommy Thompson has now joined the ADS board. He told Americans during an interview with CBS Market Watch that ID chips inserted into our bodies will be a giant step towards achieving an electronic medical record for all Americans.86 While ADS is donating to medical facilities expensive scanners required to read its subdermal chips,87 the Department of Health and Human Services is providing grants to medical providers who will help build electronic health records for Americans within a decade.88 ADS and its subsidiaries, including VeriChip Corporation, have developed several kinds of implantable subdermal chips. One type is the FDA-approved VeriChip, that spits out the implantee's ID number when it is scanned by a chip reader. Another is the VeriPay device which carries financial information and is scanned like a debit card. People in Europe are now being implanted with VeriPay chips in order to enter bars and nightclubs.89 So far, these kinds of chips are passive. That is, they don't beam information continuously. Their transponders have to be awakened by a reader. These chips and their scanners pass kilohertz radio-frequency signals back and forth through the skin. The first step to inducing public acceptance of these ID chips, said San Francisco Gate columnist Mark Morford, is getting the public to accept chip implants as beneficial for health. The next step is to make it all fun and commercial and convenient. The third step is "whatever the hell they want."90 VeriChip Corporation recently announced that already 68 U.S. medical facilities, including 65 hospitals, have now agreed to implement its VariMed system for patient and staff identification and tracking.91 This includes both implantable and wearable ID chips that will tie the health records of patients into Big Brother's electronic national database. In New Jersey, Hackensack University Medical Center and Trinitas Hospital, will be implanting patients in their emergency rooms.92 These crafty hucksters are targeting the most vulnerable people first-- the injured and the sick who are desperate for care, plus the homeless and mentally retarded who can't defend themselves. Sensornet As injectable ID chips come on line, Homeland Security is paying numerous corporations to develop a national network of object-mounted wireless sensors that will be able to read implanted human chips.93 This network of sensors will eventually relay information on the whereabouts and activities of implantees to teams of surveillance specialists. Conceivably, every wall socket could become a reader for implanted chips. To quote University of Kansas professor Jerry Dobson, these devices will ultimately offer "a new form of human slavery based on location control. They pose the greatest threat to personal freedom ever faced in human history."94 The argument that implanted chips will protect people from identity theft recently evaporated when researcher Jonathan Westhues demonstrated on the Internet how easy it is to decode a VeriChip number implanted in a person's arm and then program another chip with that same number.95 Digital Angel: Fascist Big Brother's most cool tool Passive ID subdermal chips are the "good news" compared to grotesque ACTIVE implant chips also developed by ADS. The implantable Digital Angel is a grotesque communication device that can continually relay information wirelessly to either ground stations or to satellite systems.96 Developed to be a true tracking chip like the bulky radio ankle bracelets locked onto prisoners, it is tiny enough to be implanted into human flesh. The Angel has a built-in GPS receiver and a wireless transceiver. In December, 2004, ADS signed an agreement with the satellite telecommunications company ORBCOMM. Such collusion will one day turn implanted citizens into walking radio beacons, trackable by satellite.97 Digital Angel is the ultimate in totalitarian control, to date Big Fascist Brother's most "cool tool." Cooler tools now in R&D ADS has also developed a new Bio-Therm chip implant which can read and transmit to monitoring devices a person's temperature. In the works are other chips for identifying blood pressure, disease and hormonal levels.98 Reportedly, these biochips will be capable of relaying information to both satellite and ground stations. Oracle is backing a powerful new 999 medical biochip that contains a Pentium microprocessor just 2mm square. This computerized sensor is being implanted into diabetics by doctors experimenting in London.99 Text messages from the chip's sensors will travel through flesh to a cell phone tethered to the patient, then on to monitoring stations. Odorless, colorless-wireless In 2000, ADS chairman Richard Sullivan said that Digital Angel "relates directly to the exploding wireless marketplace." He added, "We'll be demonstrating for the first time ever that wireless telecommunications systems and bio-sensor devices-capable of measuring and transmitting critical body function data-can be successfully linked together with GPS technology and integrated with the internet."100 Most sinister is the fact that these chips can be "activated" by distant monitoring facilities and they can be "written to" wirelessly, allowing the fascists to furtively add information that the chip bearer may know nothing about.101 Powerful web-enabled tracking chips which send and receive information at long distances are ultra radiation-intensive. Big Brother's most cool tool is "hotter" than Hades. Bodies bearing these chips will be continuously bombarded with incoming and outgoing microwave radiation, most likely in the megahertz or gigahertz range, the same frequencies employed by cell phones. Satellites communicate in microwave frequencies. Last October, Time magazine gave a plug to implantable ID and bio chips, stating they could save lives.102 But people who have active chips imbedded in their bodies will be dead men walking. The human body is not compatible with microwave radiation and bodies subjected to it 24-7 will ultimately be destroyed. The fascists know this but, as Sullivan explained, the mighty global surveillance system now under construction is absolutely dependant upon wireless microwave transmissions. This is precisely why Americans have never been told the terrible truth about what hand held wireless devices are already doing to their health, to their fragile memory centers and to their withering immune systems.103 ...to keep us "safe" In the Homeland Security state, microchip implants of various kinds will likely become as common as cell phones. Eventually, citizens who refuse to accept identification chips may be denied access to services and benefits by heel-clickers supervising the national ID system. And thus we see how cleverly Americans are being manipulated into this crucible by killers in the White House, and by the most corrupt Congress in history and by the amoral, money-grubbing corporate megalith they all rode in on. In the name of national security and public health-millions of non-discerning citizens will allow themselves to be micro-chipped like dogs, tracked by satellite and stripped of all privacy as they become the virtual slaves of a techno-tyrannical surveillance state. If we want to know what USA will be like in the near future, we need only look at Tony Blair's Great Britain-surely the most advanced police state in Europe: ID cards with facial scans will soon be compulsory throughout U.K.104 There are over 4 million closed circuit cameras monitoring every move the British people make and all faces caught on camera can be matched with a national data bank.105 British police are carrying hand held DNA kits linked to national data bases for when they test saliva.106 People are being pulled off London trains at random and forced to submit to a full body backscatter X-ray to reveal what they have under their clothes.107 Swipe cards used for transportation and building entry allow police to plot a citizen's every move on a dot map.108 All moving vehicles in Britain are camera-recorded so that police can analyze, by license number, every journey, and every gas purchase made.109 People and vehicles are being tracked from cell towers with a new technology called "Celldar" (as in radar).110 The British people are reporting grave illnesses from their exposure to thousands of microwave transmitters which make this metastasizing surveillance nightmare possible.111 Preview of Part 2 and a few helpful hints In part two of this discussion, we will document the latest scientific information on the devastating health effects that will result from the implanted microwave devices used to track and control slaves of the state. If you feel a creeping allergy to the fascism we have documented here, you can do something about it now. Make the choice right now to keep microwave-driven wireless devices as far away from your body as you can get them. These devices include all wireless telephones-both cell and household cordless-plus wireless computers, headphones and all other gadgets empowered by megahertz or gigahertz frequencies. If you must use wireless phones for business or emergencies, use speaker phones only. Never put a wireless device on your body, least of all near your precious brain. You are going to NEED a brain to survive-and ultimately defeat-fascist America. Microwave transmitters are not toys; they are weapons. Brother's wireless revolution has induced millions of fools to voluntarily point these weapons at their own heads. The wireless revolution is not only about money, it is about control. It is about acclimatizing the masses to accept the dehumanizing parameters of Orwellian surveillance. A police state best flourishes when its citizens are sick, dimwitted cyborgs who are easy to track and control. The "cool tool" communications microchip can also be used by the fascists to impose behavior modification. The CIA has decades of experience in using various microwave frequencies to misalign and confound the human brain in order to trigger prescribed behavior patterns.112 As the police state broadens with the help of Homeland's cooperating telcom players, it is conceivable that such devilish frequencies could be used with evil intent against all those who are "connected." These hapless victims, driven to and fro by fascist propaganda, will be oblivious to what is channeled into their sizzling brain neurons, into their internal organs, into their very souls by the deadly wireless transceivers they bear in their flesh. Peter Zhou, chief scientist for the development of Digital Angel, declared that the subdermal identification/communication implants will make humans "a hybrid of electronic intelligence and our own soul."113 He is right! America's parasitic police state and all of its perversions absolutely ARE a soul thing. So the time has surely come to stand back and scrutinize this illicit monstrosity which so brazenly deceives, swindles, sickens and murders the people to gain power and wealth. Please start thinking about how you and your family are going to exist for a time in a demon-driven world where deadly radio frequency identification implants become mandatory. The more people who courageously resolve to stand firm against this mighty beast, the safer we will be until we get through this miserable, and hopefully final fascist interlude in human history. NOTES 1. "Senator Reid Calls U.S. Congress the Most Corrupt in History," T. Ferraro, Reuters, 12-18-05. 2. "Alito a Threat to our Fundamental Rights," speech on Senate floor by Senator Patrick Leahy 1-24-2006. 3. Wilson quoted in a letter to William Rivers Pit, "The Bunker Mentality," Truthout Perspective, 11-24-05. 4. "The $4 Billion Industry That is America's Guilty Secret," Robert Cornwell, The Independent, UK, 1-4-06. 5. "The March of the Straw Soldiers," New York Times, Op. ed 2-2-06. 6. "Police State," Kelly O'Meara, Insight on the News, 11-9-01. 7. "The Homeland Security Monstrosity," Rep. Ron Paul, Ron Paul Archives, 11-19-02. 8. "You are A Suspect," William Safire, New York Times, Op. ed. 11-14-02. 9. "The Homeland Security Monstrosity," Paul, op. cit. 10. Wall Street and the Bolshevik Revolution, Dr. Antony C. Sutton, Arlington House, 1974; also How the Order Creates War and Revolution, Dr. Antony C. Sutton, 1984. 11. Ibid. 12. Ibid. 13. Wall Street and the Rise of Hitler, Dr. Antony C. Sutton, 1976. 14. "How Bush's Grandfather Helped Hitler Rise to Power," The Guardian, UK., B. Aris and D. Campbell, 8-31-05. Find this article at Rense.com.; also "The Best Enemies Money Can Buy," Michael C. Ruppert, www.fromthewilderness.com, 10-9-2001. 15. "Bush Nazi Dealings Continued Until 1951-Federal Documents," J. Buchanan and S. Michael, The New Hampshire Gazette, Vol. 248, No. 3, 11-7-2003. 16. George Bush: The Unauthorized Biography, Webster Tarpley, Executive Intelligence Review, 1992. 17. "Intelligence Bill Is A New Agenda, Not Reform," World Affairs Brief, Joel Skousen, 12-10-04. 18. "America Drifts Rapidly Toward A Police State," Mike Whitney, Zmag.org 11-5-05. See rense.com. 19. Ibid. 20. "Chertoff Moves For Total Personal Information Control," Siobhan Gorman, rense.com 5-5-05. 21. "US Plans Massive Data Sweep," M. Clayton, The Christian Science Monitor, 2-9-06. 22. "Feds Warn of People too Antsy, Calm or Pale," Spokesman Review, 5-27-2003. 23. "Pentagon Expanding Its Domestic Surveillance Activity," W. Pincus, The Washington Post, 11-27-2005. 24. "The Other Big Brother," Newsweek, January 30, 2006; "Pentagon's Intelligence Authority Widens," Washington Post, 12-19-2005. 25. "Spying on the Protestors," The Nation, August 2005. Professor Pyle, a former investigator for Senator Frank Church's Select Committee on Intelligence, now teaches at Mt. Holyoke College. 26. "When the Feds Come Knocking," Steve Weissman, truthout.org, 8-23-2004. 27. "Top Officials Say Rumsfeld Trying to Make Foreign Policy," Knight Rider, Spokesman Review, May 2005. 28. "Pentagon Has New Espionage Unit," Washington Post 1-24-05. 29. "Republicans See Signs that Pentagon is Evading Oversight," D. Jehl, The New York Times, 9-29-05. 30. "Paranoia Grips Bush Cabal, Eric Margolis, Toronto Sun, 2-6-05. 31. "NSA Whistleblower Alleges Illegal Spying," ABC News, 1-10-06; also: "Bush Authorized Domestic Spying Before 9-11," Jason Leopold, Truthout Perspective, 1-13-2006; also: "This is Big Brother Run Amok," Knight Rider, Spokesman Review, 12-17-05. 32. "On the President's Warrantless Wiretapping Program," by Senator Russ Feingold, As prepared for delivery from the Senate floor, 2-7-06. 33. "Spy Agency Data After September 11 Led FBI to Dead Ends," L. Bergman, The New York Times, 1-17-2006. 34. "State's Muslims Being Questioned-ACLU Offers Seminar," 9-12-2004. 35. "Surveillance Net Yields Few Suspects," Washington Post, 2-05-2006. 36. Ibid. 37. "Congress Increases Agency Authority to Mandate Medical Intervention," Idaho Observer, 12-16-2005; also "Projects Bioshield, BioWatch and BioSense-- the Diabolical Creation of a Mandated Marketplace," Idaho Observer, 1-18-2005. 38. "Hastert, Frist Said to Rig Bill for Drug Firms," B. Theobald, The Gannett News Service 2-09-2006. 39. Vaccine A-The Covert Government Experiment That's Killing Our Soldiers and Why GI's are Only the First Victims, Gary Matsumoto, Basic Books, 2004. 40. Ibid. 41. "An Enemy of the State," Doug Thompson, www.capitolhillblue.com, 11-7-2005. 42. "Author of 'Bush's Brain' Put on No-Fly List," Maccabee, 1-05-2006, Bio at Huffington Post, www.dailykos.com. 43. "Homeland Security Opening Private Mail," B. Meeks, MSNBC.com, 1-6-06. 44. "Feds Use ISPs to Spy on Internet Users," Nick Parker SLYCK.com 11-13-05; also "Colleges Protest Call to Upgrade Online Systems," S. Dillon, The New York Times, 10-23-05. 45. "Feds After Google Data," H. Mintz, Mercury News, 1-19-06. 46. "The FBI's Secret Scrutiny," The Washington Post, B. Gellman, 11-6-05. 47. "NSA Used City Police to Track Peace Activists," D. Birch, The Baltimore Sun, 1-13-06; also "California Guard Probed by US--Peace Activists Say Unit is Spying," Associated Press, 7-7-05; also "Look Who's Spying On Your Granny," The Sacramento Bee editorial, 6-29-05. 48. "Wal-Mart Gives Teen's Anti-Bush Poster to Police," Matthew Rothschild, The Progressive, 10-8-05. See rense.com. 49. "Professor Thinks Bombs, Not Planes, Toppled WTC," Deseret Morning News, E. Jarvik, 11-10-2005; also 9-11 Demo: "BYU's Prof. Jones Has Wide Academic Support," Greg Szymanski, 11-15-05, see rense.com. 50. "Former Top German Minister Rejects Official Story of 9-11 Attacks," Tagesspiegel, 1-13-2002. 51. "International Terrorism Does Not Exist," General Leonid Ivashov, 1-22-06. See rense.com. 52. Transcript: Alex Jones Interviews Stanley Hilton, The Alex Jones Show3-11-2003. 53. Ibid. 54. Crossing the Rubicon, Michael C. Ruppert, New Society Publishers, 2004. See Chapter 16, Silencing Congress. 55. Ibid. 56. Ibid. 57. "US Mulls Federal Troops for Bird Flu Quarantine," Reuters, 10-12-2005; also "Bush Could Seize Absolute Control of U.S. Government," Doug Thompson, Capitol Hill Blue, 1-14-06. See Rense.com. 58. "Bush's Erratic Behavior Worries White House Aides," Doug Thompson, Capitol Hill Blue, 6-4-04;also "Is Bush Out of Control? Said on Anti-Depressants," Doug Thompson, Capitol Hill Blue, 8-15-05. 59. Bush on the Couch, Dr. Justin Frank, Regan Books, 2004. 60. "Pentagon Used White Phosphorus in Iraq", Associated Press, 11-16005; also "I Treated People Who Had their Skin Melted," Dahr Jamail, The Independent, UK.11-15-05. 61. "Battlespace America," P. Byrne, Mother Jones, May/June 2005. 62. "Military Unprepared for 9-11 Attacks," S. Waterman, United Press International, 5-23-03. Despite two entire squadrons of combat-ready fighter jets at Andrews Air Force Base 10 miles from the Pentagon, and despite ample warning, not a single jet was dispatched to protect D.C. on 9-11. 63. "Top Secret Pentagon Operation 'Granite Shadow' Revealed," W. Arkin, Washington Post, 9-25-05. 64. "Martial Law No Longer On the Horizon: It's Already Here," S. Watson, Prison Planet, 12-15-05. 65. "Gen. Franks, Doubts Constitution Will Survive WMD Attack," J. Edwards, NewsMax.com, 11-21-03. Gen Max interviewed by Cigar Aficionado Magazine, Nov. 2003. 66. "War Plans Drafted to Counter Terror Attacks in US," B. Graham, The Washington Post, 8-8-05. 67. "Halliburton Detention Camps for Political Subversives," Paul J. Watson, Prisonplanet.com, 2-1-06; also "Bush's Mysterious New Programs," N. Parry, Consortium News, 2-21-06. 68. The World Order-A Study in the Hegemony of Parasitism, Eustace Mullins, 1985. 69. "Videos Challenge Accounts of Convention Unrest," Jim Dwyer, New York Times, 4-12-05. 70. "Mission: Technology-- CIA Backing Promises Technologies to Keep Spies On Top," Spokesman Review, 1-21-2002. 71. Softwar-- An Intimate Portrait of Larry Ellison and Oracle, Matthew Symonds, Simon and Schuster, 2003. The CIA became Oracle's first customer after the company was founded in the late 1970's. 72. "National ID Card Idea Attracting Highest-Level Support," Ackerman and Rogers, San Jose Mercury News, 10-18-01. 73. Softwar-- An Intimate Portrait of Larry Ellison and Oracle, op. cit. 74. "Your Papers Please-- US Adopts National ID: Homeland Security Now in Charge of Regulations for all US States Drivers Licenses and Birth Certificates," Jonathan Wheeler 12-9-04. See rense.com. 75. Ron Paul's Freedom Report, June 2005 "National ID Cards Won't Stop Terrorism or Illegal Immigration." 76. "Your Papers Please," Wheeler, op. cit. 77. "Government Secrecy Swells, Report Says," Associated Press, Spokesman Review, 9-4-05. 78. Policy Analysis, A National ID System, Cato Institute, Stephen Moore, 9-7-95. 79. "Implantable Chip Offers Medical Information, Privacy Worries," Associated Press, Spokesman Review, 10-14-04. 80. "IBM Calls for Global Identity System," V. Yeo, ZDNet Asia 11-10-05. To review IBM financial support of ADS, see "Applied Digital Gets Reprieve From Creditor," World Net Daily, 3-28-03. 81. "How IBM Helped Automate the Nazi Death Machine In Poland," E. Black, Village Voice.com 3-27-02. 82. "Meet the Digital Angel From Hell," World Net Daily, 2-14-2000. 83. "RFID Gets Skin-Deep Alternative," J. Best, silicon.com 8-5-04. See rense.com. 84. "Bio-Chip Featured At Government Health Showcase," World Net Daily, 4-29-04. 85. "FDA Approves Implantable Chip Sales in Humans," Wired.com, 10-24-02; also"Implantable Chip's Medical Dangers," World Net Daily, 10-20-04. 86. "Tommy Thompson Refuses To Get Chipped," SpyChips.com, 12-9-05. 87. "US. To Weigh Computer Chip Implant," C. Newton, Associated Press, 2-26-02. 88. "Implantable Chip Offers Medical Information, Privacy Worries," Associated Press, Spokesman Review, 10-14-04. 89. "Paying for Drinks with Wave of the Hand," S. Gossett, World Net Daily 4-14-04. 90. "Big Brother Under Your Skin," M. Morford, sfgate,com, 10-20-04. 91. "VeriChip Corporation Expands Adoption of VeriMed System for Patient Identification, VeriChip News Release, 12-1-05. 92. "VeriChip Expands Hospital Infrastructure: Hackensack University Medical Center Becomes the Second Major Medical Center to Adopt the VeriChip System," infowars.net, 3-16-05; also "Trinitas To Test RFID Implants," mobilehealthdata.com. 8-22-05. 93. "Sensor Everywhere-A "Bucket Brigade" of Tiny, Wireless Sensors May Be Able to Track Anything, Anytime, Anywhere," A. Ricadela, Information Week, 1-24-05. 94. "Human Tracking Goes Mainstream," Jerry Dobson, Directions Magazine, 1-27-05. 95. "Demo: Cloning a VeriChip," http://cq.cx/verichip.pl.; See also "VeriChip RFID Implant Hacked," K. Albrecht and L. McIntyre, Spychips.com, 1-28-06, rense.com. 96. "Post-9-11 Security Fears Usher In Subdermal Chips," World Net Daily, 2-4-02. 97. "People Tracking Closer to Reality," World Net Daily 12-23-04. 98. "GPS Implant Makes Debut," S. Gossett, World Net Daily, 5-14-03. 99. "Patients Get 999 Chip Implants," timesonline.co.uk, 6-12-05. 100. "Digital Angel Human ID Implant To Be Unveiled in October-2 Months Early," J. Kohlbrand and J. Foster, World Net Daily, 8-13-00. 101. "Mark of the Beast?" World Net Daily, 1-28-02. 102. "Biochips for Everyone!" D. Fonda, Time Magazine, www.time.com, 10-16-05. 103. Cell Phones, Invisible Hazards In the Wireless Age, Dr. George Carlo, Carroll and Graf Publishers, 2001. 104. "UK ID Cards 'Defeated' Yet Going Ahead," S. Watson, infowars.net, 1-24-06. 105. "Big Brother Britain, 2004--Four Million CCTV Cameras Watch Public," Independent, UK. 1-12-04. 106. "Roadside DNA Tests On Citizen Planned," D. Cracknel, Telegraph, UK, 12-10-00. See rense.com. 107. "New Body Screeners In Use in London: We are Living in a Dystopian Nightmare," S. Watson, Inforwars.net, 1-12-06. 108. No Longer Lost In the Crowd: Prospects of Continuous Geosurveillance, M. Dodge and M. Batty, Center For Advance Spatial Analysis, University College London, March 2004. 109. "Britain Will Be First Country to Monitor Every Car Journey," The Independent, UK, 12-21-05. 110. "How Mobile Phones Let Spies See Our every Move," J. Burke and P. Warren, The Observer. UK, 10-14-02. 111. An excellent website for European reports of microwave health effects is: http://www.buergerwelle.com. Check these archives and read for a year! 112. "Microwave Detection-Remote Mind Control Technology," Anna Keeler, reprinted from Secret and Suppressed: Banned Ideas and Hidden History, edited by Jim Keith. This is an excellent history of Operation Pandora, part of the Pentagon's multi-faceted research project using microwave frequencies to induce both physical and mental illness. 113. "Digital Angel Set To Fly Tomorrow," World Net Daily, 6-14-01. |
|
By Karen Rouse
Denver Post Staff Writer 2 Mar 06 An Overland High School teacher who criticized President Bush, capitalism and U.S. foreign policy during his geography class was placed on administrative leave Wednesday afternoon after a student who recorded the session went public with the tape.
In the 20-minute recording, made on an MP3 player, teacher Jay Bennish described capitalism as a system "at odds with human rights." He also said there were "eerie similarities" between what Bush said during his Jan. 28 State of the Union address and "things that Adolf Hitler used to say." The United States was "probably the single most violent nation on planet Earth," Bennish also said on the tape. Bennish, who has been part of Overland's social studies faculty since 2000, did not return calls seeking comment Wednesday. Cherry Creek School District officials are investigating the incident, but no disciplinary action has been taken, district spokeswoman Tustin Amole said. Bennish was placed on leave "to take some of the pressure off of him" during the investigation, which could wrap up in a week, Amole said. Superintendent Monte Moses, who received a copy of the recording on Monday from 850 KOA-AM radio show host Mike Rosen, said it appears "a breach of district policy" occurred. "Our policy calls for both sides to be present ... in the interest of intellectual discourse," Moses said. Bennish's presentation appeared to be unbalanced, he said. The district is looking into whether the incident was an isolated one and will ensure that a balanced viewpoint of the president's State of the Union address is provided to students, Moses said. Moses also said the district will be fair to Bennish. "People in life make mistakes occasionally," he said. "We address them. We learn from them." The 20-minute recording of only a portion of the class was made by 16-year-old sophomore Sean Allen the day after the president's speech. The recording has raised questions about what level of academic freedom is acceptable for high school teachers. It also has generated discussions about Bennish on dozens of websites. Sean, who appeared on Rosen's show Wednesday morning, said in an interview he had been disturbed by the "political rants" he heard in Bennish's class. He added that he wanted to tape the session for his father, who later shared it with the media. Sean, who described himself as a political independent, said the comments seemed inappropriate for a geography class. "If he wants to give an opinion in class, I'm perfectly OK with that," he said. "But he has to give both sides of the story." James McGrath Morris, an author who has written about academic freedom issues, said Bennish's comments are acceptable for an adult audience, but they are hard to defend in a high school classroom. In a number of legal cases, courts have ruled that "up until the age of majority, children are easily influenced ... in a way that they don't have the faculties to sort out rights from wrongs," Morris said. Staff writer Karen Rouse can be reached at 303-820-1684 or krouse@denverpost.com Comment: We hope readers will join us in emailing the journalist who wrote this article and the newspaper and reminding them that this teacher has been suspended for speaking the truth. Her email address: krouse@denverpost.com
|
Have a question or comment about the Signs page? Discuss it on the Signs of the Times news forum with the Signs Team.
Some icons appearing on this site were taken from the Crystal Package by Evarldo and other packages by: Yellowicon, Fernando Albuquerque, Tabtab, Mischa McLachlan, and Rhandros Dembicki.
Remember, we need your help to collect information on what is going on in your part of the world!
Send your article suggestions to: 
Contact Webmaster at signs-of-the-times.org
Cassiopaean materials Copyright ©1994-2014 Arkadiusz Jadczyk and Laura Knight-Jadczyk. All rights reserved. "Cassiopaea, Cassiopaean, Cassiopaeans," is a registered trademark of Arkadiusz Jadczyk and Laura Knight-Jadczyk.
Letters addressed to Cassiopaea, Quantum Future School, Ark or Laura, become the property of Arkadiusz Jadczyk and Laura Knight-Jadczyk
Republication and re-dissemination of our copyrighted material in any manner is expressly prohibited without prior written consent.
The Gladiator: John Fitzgerald Kennedy
John F. Kennedy and All Those "isms"
John F. Kennedy, J. Edgar Hoover, Organized Crime and the Global Village
John F. Kennedy and the Psychopathology of Politics
John F. Kennedy and the Pigs of War
John F. Kennedy and the Titans
John F. Kennedy, Oil, and the War on Terror
John F. Kennedy, The Secret Service and Rich, Fascist Texans
Recent Articles:
New in French! La fin du monde tel que nous le connaissons
New in French! Le "fascisme islamique"
New in Arabic! العدوّ الحقيقي
New! Spiritual Predator: Prem Rawat AKA Maharaji - Henry See
Top Secret! Clear Evidence that Flight 77 Hit The Pentagon on 9/11: a Parody - Simon Sackville
Latest Signs of the Times Editorials
Executing Saddam Hussein was an Act of Vandalism
Latest Topics on the Signs Forum |
Signs Monthly News Roundups!
June 2005
July 2005
August 2005
September 2005
October 2005
November
2005
February 2006
March 2006
April 2006
May 2006
June 2006
July 2006
August 2006
September 2006



![Validate my Atom 1.0 feed [Valid Atom 1.0]](/signs/images/valid-atom.png)